Lawmakers and legal observers said it was deeply alarming that Trump’s DOJ even tried to secure the indictment.
Honest, paywall-free news is rare. Please support our boldly independent journalism with a donation of any size.
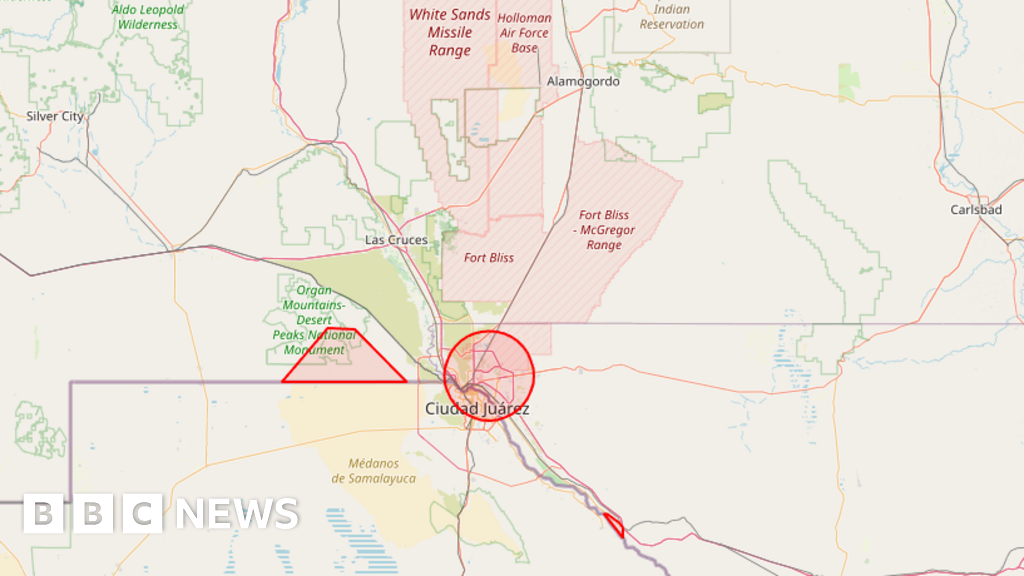
A federal grand jury on Tuesday declined to go along with an effort by the Trump Justice Department to indict Democratic lawmakers involved in a November video reminding members of the US military of their duty to refuse illegal orders, a message that came as President Donald Trump deployed troops to major American cities.
The failed attempt to indict the six Democratic lawmakers was led by Trump loyalist Jeanine Pirro, a former Fox News host who is now serving as US attorney for the District of Columbia. The New York Times reported that federal prosecutors “sought to persuade the grand jurors that the lawmakers had violated a statute that forbids interfering with the loyalty, morale, or discipline of the US armed forces.”
Trump, who has repeatedly weaponized the Justice Department against his political opponents, erupted in response to the 90-second video, accusing the Democratic lawmakers behind it of “seditious behavior, punishable by death.”
The lawmakers who appeared in the video were Sens. Mark Kelly of Arizona and Elissa Slotkin of Michigan as well as Reps. Jason Crow of Colorado, Chrissy Houlahan and Chris Deluzio of Pennsylvania, and Maggie Goodlander of New Hampshire. The Democrats learned they were under investigation last month when they received inquiries from Pirro’s office.
Lawmakers and legal observers said it was deeply alarming that the DOJ even tried to secure the indictment.
“What an ugly assault on the First Amendment and on Congress,” said legal scholar Ryan Goodman. “Thankfully, thwarted.”
Kelly, a retired Navy captain who is facing Pentagon attempts to censure him and cut his military benefits, said the effort to indict him and his fellow Democratic lawmakers was “an outrageous abuse of power by Donald Trump and his lackies.”
“It wasn’t enough for Pete Hegseth to censure me and threaten to demote me, now it appears they tried to have me charged with a crime — all because of something I said that they didn’t like,” Kelly wrote on social media. “That’s not the way things work in America.”
We want to speak directly to members of the Military and the Intelligence Community.
The American people need you to stand up for our laws and our Constitution.
Don’t give up the ship. pic.twitter.com/N8lW0EpQ7r
— Sen. Elissa Slotkin (@SenatorSlotkin) November 18, 2025
Slotkin, a former CIA officer who organized the November video, said Pirro pursued the indictment “at the direction of President Trump, who said repeatedly that I should be investigated, arrested, and hanged for sedition.”
“Today, it was a grand jury of anonymous American citizens who upheld the rule of law and determined this case should not proceed. Hopefully, this ends this politicized investigation for good,” the senator said. “But today wasn’t just an embarrassing day for the administration. It was another sad day for our country.”
“Because whether or not Pirro succeeded is not the point. It’s that President Trump continues to weaponize our justice system against his perceived enemies,” Slotkin added. “No matter what President Trump and Pirro continue to do with this case, tonight we can score one for the Constitution, our freedom of speech, and the rule of law.”
Speaking against the authoritarian crackdown
In the midst of a nationwide attack on civil liberties, Truthout urgently needs your help.
Journalism is a critical tool in the fight against Trump and his extremist agenda. The right wing knows this — that’s why they’ve taken over many legacy media publications.
But we won’t let truth be replaced by propaganda. As the Trump administration works to silence dissent, please support nonprofit independent journalism. Truthout is almost entirely funded by individual giving, so a one-time or monthly donation goes a long way. Click below to sustain our work.