(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Source link
Category: Uncategorized
-
ISC Stormcast For Tuesday, March 24th, 2026 https://isc.sans.edu/podcastdetail/9862
-

Myanmar’s Three Brotherhood Alliance Splits Under China’s Influence
Welcome to Foreign Policy’s Southeast Asia Brief.
The highlights this week: Myanmar’s anti-junta alliance is splitting under Beijing’s influence, Vietnam conducts its first-ever live-fire joint exercises with China, Malaysia’s Iranian double game on oil, and why Indonesians are scrubbing their cats.
Have feedback? Hit reply to let me know your thoughts.
Myanmar’s Anti-Junta Alliance Turns on Itself
On March 16, news broke that the Myanmar National Democratic Alliance Army (MNDAA) had seized Kutkai, in northern Shan State—not from Myanmar’s ruling junta, but rather from the Ta’ang National Liberation Army (TNLA).
What prompted the MNDAA to turn on its erstwhile ally? Both groups are part of the Three Brotherhood Alliance that launched Operation 1027, which brought the junta to its knees in 2023 and 2024.
Since March 19 it seems a cease-fire has been established—though outstanding issues apparently remain.
The MNDAA claims the cause was the TNLA attacking MNDAA troops on patrol on March 14. The two groups do have a history of skirmishing for territory.
Others point to China—which, as last week’s newsletter highlighted, exerts a growing influence over the MNDAA.
“It seems to me the MNDAA is becoming a tool for China’s strategic interests in northern Myanmar,” Angshuman Choudhury, a researcher focusing on Myanmar, told Foreign Policy.
The significance of Kutkai is that it lies on a long highway that connects Chinese Yunnan to central Myanmar, which is still under the control of the military. The TNLA had apparently operated checkpoints there, holding up trucks, Choudhury said.
An unblocked road could let commerce flow more freely and could help stabilize the junta as it transitions to a new political setup. This would suit China, a former patron of the Three Brotherhood Alliance now backing the junta for fear of a failed state on its border.
The fact that China seemingly hasn’t leaned on the MNDAA to stop its aggression—which also included drone strikes near Namkham—suggests it approves of it, Choudhury said.
“China told the FPNCC [Federal Political Negotiation and Consultative Committee, an alliance of ethnic armed organizations] not to intervene and mediate,” he added.
Why the MNDAA might be more susceptible to Chinese pressure than its fellow ethnic armed organizations is unclear, though a few factors might be noted.
The MNDAA is a splinter of the Burmese Communist Party, with long historic links to China. Its members are predominantly Kokang Chinese—Mandarin-speaking ethnic Chinese.
Also, China has in the recent past yanked the leash briefly, detaining the leader of the MNDAA in 2024 and 2025.
The strategic gain of an unlocked highway to China comes at a good time for the Myanmar junta.
Following a January show election, Myanmar’s new parliament sat for the first time on March 16.
A new president—tipped as junta leader Min Aung Hlaing—will soon be selected. And there are signs of a softening of diplomatic positions toward it in the region.
China-Vietnam ties strengthen. China and Vietnam conducted their first-ever live-fire joint exercise on March 17.
Two frigates from each country were involved in the joint exercise, which took place in the Beibu Gulf, which straddles southern China and Vietnam.
The exercise coincided with the two navies’ 40th joint patrol and 10th China-Vietnam Border Defense Friendship Exchange.
More notably, it also coincided with visits of three top Chinese officials—Minister of Foreign Affairs Wang Yi along with the Minister of National Defense and Minister of National Security—who met with Vietnam’s leader, To Lam, as well as their Vietnamese ministerial counterparts.
Nhan Dan, the official newspaper of the Vietnamese Communist Party, declared the new 3+3 dialogue showed “a high level of political trust and increasingly profound strategic collaboration” between the two countries.
Vietnam has also pursued a closer relationship with the United States, too, even joining President Donald Trump’s Board of Peace.
But a recent announcement by Nhan Dan on the comprehensive strategic partnership with the U.S. used language a degree or two less warm.
Thai PM starts new term. On March 19, Anutin Charnvirakul was reelected to his position as prime minister.
His cabinet will be announced shortly, but it is widely expected that the technocrats holding the finance, foreign, and commerce portfolios will remain in place, with various politicians filling other positions.
With his coalition holding 293 of 498 votes, Anutin’s position looks strong. But the government is facing an energy crisis, with Thailand particularly exposed to the disruptions of the Iran war.
Diesel shortages have been reported across the country. The opposition is already trying to make hay.
Another issue is that on March 18 the Constitutional Court announced it had accepted a case that could potentially annul the election results. Filed by the Thai ombudsman, the case hinges on barcodes on ballots cast during the election.
Critics say the barcode could be used to identify voters. The Election Commission says the barcodes boosted security and no one could be identified without other information that is securely stored.
Thai courts annulled the election in 2006 on the grounds the ballot had not been secret.
However, the political context was very different then, with a military-royalist elite pushing back against a populist victory. In this most recent election, conservative forces triumphed.
Spring cleaning your cats. In Indonesia in the run-up to Eid—known locally as Hari Raya—the traditional thing is to give everything a thorough scrub.
With the relatives and neighbors coming around, you prepare by cleaning the good teak furniture, dusting the curtains in the living room, and polishing up the fancy china.
Now a new item is getting added to that list: cats. Indonesian social media, like the rest of the world long dominated by feline content, is ablaze with videos of people scrubbing and shampooing furry companions ahead of the big day.
Cats have long been a favored animal in Islam. Various hadiths attest to the prophet’s love of them. Mu’izza is a particularly popular cat name in Indonesia—allegedly the name of Mohammed’s own beloved pet.
But in animal-loving Indonesia, cats seem especially beloved.
A recent survey found that almost half of all Indonesian households own a cat. Meanwhile, industry estimates suggest spending on pets is growing at about 10 percent a year.
A cat can even be a political tool. President Prabowo Subianto’s secret weapon when he campaigned for president in 2024 was a cat called Bobby. Inevitably, the cat’s official Instagram account has posted a tasteful Eid greeting.
Religious officials and experts use telescopes and modern imaging devices to see the new moon to determine the end of Ramadan in Perlis, Malaysia, on March 19. Religious officials and experts use telescopes and modern imaging devices to see the new moon to determine the end of Ramadan in Perlis, Malaysia, on March 19.Photo by Farid Bin Tajuddin/Anadolu via Getty Images
The date of Eid is set by a lunar calendar and based on the sighting of a new crescent moon. This can create an interesting theological conundrum. Do you celebrate Eid when you see the moon? Or, if it’s overcast, do you still celebrate on a set day based on astronomical calculations?
FP’s Most Read This Week
Despite the war, Iran’s shadow tanker fleet continues business as usual in Southeast Asia, by Lu Wei Hoong and Hadi Azmi in the Straits Times.
“ASEAN’s traditional diplomatic habits—consensus, quiet consultation and the much-invoked ‘ASEAN Way’—may no longer be sufficient on their own.” John Blaxland and Noor Huda Ismail argue for a more muscular Association of Southeast Asian Nations in the Jakarta Post.
What a nice time to have a surplus. James Guild digs into Singapore’s 2026 budget in the Diplomat.
In Focus: Malaysia’s Iranian double game?
As Iran continues its blockade of the Strait of Hormuz, ships from a few countries are being allowed through. One of those countries is Malaysia, alongside China, India, Iraq, and Pakistan—according to reporting by the New York Times.
While Malaysia is a major fossil fuel producer, it still imports oil. Prime Minister Anwar Ibrahim has said about 50 percent of national imports pass through the strait.
Whether a trickle of these imports still coming through to Malaysia will be able to blunt price rises remains to be seen. Regardless, Iranian oil—now subject to a sanctions waiver by the U.S., which is desperate to keep prices down—will be in hot demand.
The fact that Malaysia is allowed through the strait reflects warm ties between the two countries.
In Southeast Asia, Muslim-majority Malaysia has been the loudest voice criticizing the U.S. and Israel’s strikes on Iran—in keeping with its long-standing outspokenness of Middle Eastern issues.
Traders in Malaysia have also long played a vital role as intermediaries selling embargoed Iranian oil to countries like China.
However, even as this goes on, two U.S. ships fitted with anti-mine countermeasures were pictured stopping off in the Malaysian port of Butterworth, apparently on their way to the strait, having pulled out of the region shortly before U.S.-Israeli strikes. Their anti-mine capacity could prove helpful for countering Iran’s ongoing blockade.
The minister of defense has downplayed the issue, portraying the presence of the two ships as a routine pit stop, occurring as part of Malaysia’s wide-ranging defense partnerships.
This has done little to stop the opposition and government critics from seizing on the issue and demanding clarification as to what the ships were doing there.
Critics suggested the U.S. ships’ presence contradicted Malaysia’s public criticism of the U.S. strikes on Iran—and might even endanger Malaysian ships by making them a target.
-

‘CanisterWorm’ Springs Wiper Attack Targeting Iran – Krebs on Security
A financially motivated data theft and extortion group is attempting to inject itself into the Iran war, unleashing a worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran’s time zone or have Farsi set as the default language.
Experts say the wiper campaign against Iran materialized this past weekend and came from a relatively new cybercrime group known as TeamPCP. In December 2025, the group began compromising corporate cloud environments using a self-propagating worm that went after exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. TeamPCP then attempted to move laterally through victim networks, siphoning authentication credentials and extorting victims over Telegram.

A snippet of the malicious CanisterWorm that seeks out and destroys data on systems that match Iran’s timezone or have Farsi as the default language. Image: Aikido.dev.
In a profile of TeamPCP published in January, the security firm Flare said the group weaponizes exposed control planes rather than exploiting endpoints, predominantly targeting cloud infrastructure over end-user devices, with Azure (61%) and AWS (36%) accounting for 97% of compromised servers.
“TeamPCP’s strength does not come from novel exploits or original malware, but from the large-scale automation and integration of well-known attack techniques,” Flare’s Assaf Morag wrote. “The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem.”
On March 19, TeamPCP executed a supply chain attack against the vulnerability scanner Trivy from Aqua Security, injecting credential-stealing malware into official releases on GitHub actions. Aqua Security said it has since removed the harmful files, but the security firm Wiz notes the attackers were able to publish malicious versions that snarfed SSH keys, cloud credentials, Kubernetes tokens and cryptocurrency wallets from users.
Over the weekend, the same technical infrastructure TeamPCP used in the Trivy attack was leveraged to deploy a new malicious payload which executes a wiper attack if the user’s timezone and locale are determined to correspond to Iran, said Charlie Eriksen, a security researcher at Aikido. In a blog post published on Sunday, Eriksen said if the wiper component detects that the victim is in Iran and has access to a Kubernetes cluster, it will destroy data on every node in that cluster.
“If it doesn’t it will just wipe the local machine,” Eriksen told KrebsOnSecurity.
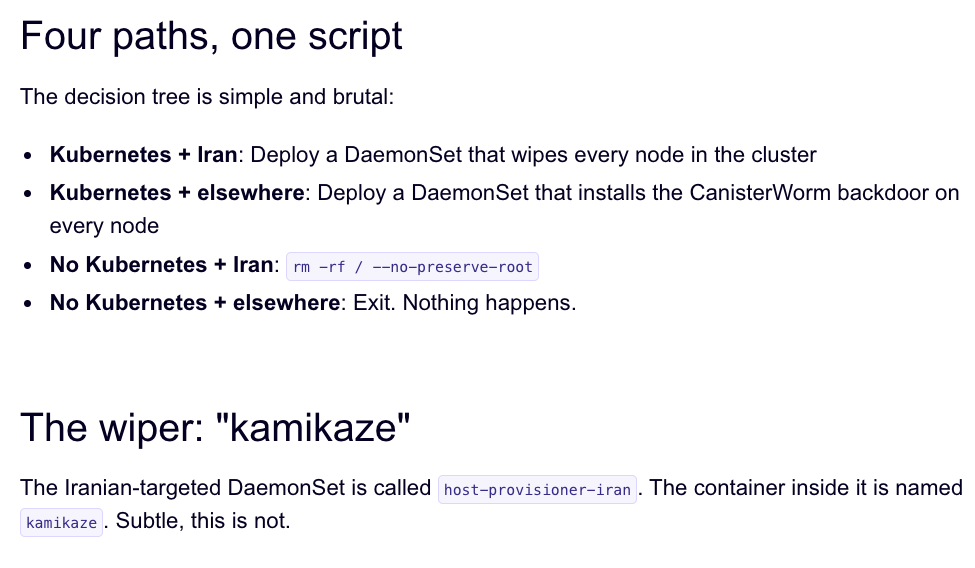
Image: Aikido.dev.
Aikido refers to TeamPCP’s infrastructure as “CanisterWorm” because the group orchestrates their campaigns using an Internet Computer Protocol (ICP) canister — a system of tamperproof, blockchain-based “smart contracts” that combine both code and data. ICP canisters can serve Web content directly to visitors, and their distributed architecture makes them resistant to takedown attempts. These canisters will remain reachable so long as their operators continue to pay virtual currency fees to keep them online.
Eriksen said the people behind TeamPCP are bragging about their exploits in a group on Telegram and claim to have used the worm to steal vast amounts of sensitive data from major companies, including a large multinational pharmaceutical firm.
“When they compromised Aqua a second time, they took a lot of GitHub accounts and started spamming these with junk messages,” Eriksen said. “It was almost like they were just showing off how much access they had. Clearly, they have an entire stash of these credentials, and what we’ve seen so far is probably a small sample of what they have.”
Security experts say the spammed GitHub messages could be a way for TeamPCP to ensure that any code packages tainted with their malware will remain prominent in GitHub searches. In a newsletter published today titled GitHub is Starting to Have a Real Malware Problem, Risky Business reporter Catalin Cimpanu writes that attackers often are seen pushing meaningless commits to their repos or using online services that sell GitHub stars and “likes” to keep malicious packages at the top of the GitHub search page.
This weekend’s outbreak is the second major supply chain attack involving Trivy in as many months. At the end of February, Trivy was hit as part of an automated threat called HackerBot-Claw, which mass exploited misconfigured workflows in GitHub Actions to steal authentication tokens.
Eriksen said it appears TeamPCP used access gained in the first attack on Aqua Security to perpetrate this weekend’s mischief. But he said there is no reliable way to tell whether TeamPCP’s wiper actually succeeded in trashing any data from victim systems, and that the malicious payload was only active for a short time over the weekend.
“They’ve been taking [the malicious code] up and down, rapidly changing it adding new features,” Eriksen said, noting that when the malicious canister wasn’t serving up malware downloads it was pointing visitors to a Rick Roll video on YouTube.
“It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention,” Eriksen said. “I feel like these people are really playing this Chaotic Evil role here.”
Cimpanu observed that supply chain attacks have increased in frequency of late as threat actors begin to grasp just how efficient they can be, and his post documents an alarming number of these incidents since 2024.
“While security firms appear to be doing a good job spotting this, we’re also gonna need GitHub’s security team to step up,” Cimpanu wrote. “Unfortunately, on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix.”
Update, 2:40 p.m. ET: Wiz is reporting that TeamPCP also pushed credential stealing malware to the KICS vulnerability scanner from Checkmarx, and that the scanner’s GitHub Action was compromised between 12:58 and 16:50 UTC today (March 23rd).
