Microsoft on Tuesday released 163 patches affecting 17 product families. Eight of the addressed issues are considered by Microsoft to be of Critical severity, and one of those is expected to be exploited within the next 30 days. Eighteen have a CVSS base score of 8.0 or higher. One – the SharePoint Spoofing vulnerability called CVE-2026-32201 – is currently known to be under active exploit in the wild, and one other (CVE-2026-33825, a Defender bug) has been publicly disclosed.
At patch time, 24 CVEs were judged more likely to be exploited in the next 30 days by the company’s estimation; that includes the Defender bug but not the SharePoint bug. Various of this month’s issues are amenable to direct detection by Sophos protections, and we include information on those in the usual table below. Unusually, our protections list also includes a patch for a Critical-severity prototype pollution bug in Adobe’s Reader and Acrobat products.
The patch load this month falls just shy of last October’s record-breaking haul, but it also includes a massive set of advisories, most of them related to Chrome patches ingested by Edge. Six advisories concern Adobe, MITRE and AMD each contribute one for Windows, Microsoft itself contributes two already-patched CVEs for Chrome/Edge, and Chrome itself weighs in with 78. The tally doesn’t quite measure up to December 2025’s mighty Mariner-flavored banquet of advisories, but combined with the patch tally, it pushes this month’s items of concern to a daunting 251. Is this a taste of patch life in the OpenClaw / Glasswing era? There’s no way of knowing that yet, but we will all be watching with interest.
We are as always including at the end of this post appendices listing all Microsoft’s patches sorted by severity (Appendix A), by predicted exploitability timeline and CVSS Base score (Appendix B), and by product family (Appendix C). Appendix D lists this month’s advisories. Appendix E provides a breakout of 127 CVEs affecting various versions of Windows Server.
Finally, we note with pleasure that Microsoft has taken to providing CWE (Common Weakness Enumeration) information for virtually all of their patches. For now, to make the most of this new transparency, we’re adding an Appendix F, in which we look at the distribution of this month’s CWEs. (Three weaknesses, by the way, account for over half of this month’s patches. To find out which three, read to the end.)
By the numbers
- Total CVEs: 163
- Publicly disclosed: 1
- Exploit detected: 1
- Severity
- Critical: 8
- Important: 154
- Moderate: 1
- Impact:
- Denial of Service: 8
- Elevation of Privilege: 94
- Information Disclosure: 20
- Remote Code Execution: 20
- Security Feature Bypass: 12
- Spoofing: 8
- Tampering: 1
- CVSS base score 9.0 or greater: 2
- CVSS base score 8.0 or greater: 18
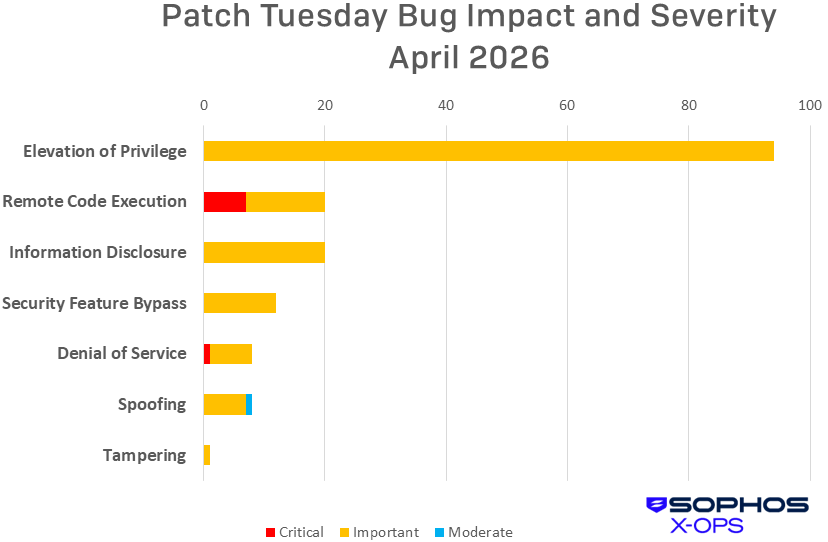
Figure 1: Elevation of Privilege represents the lion’s share of April’s CVEs, but over a third of the RCEs are Critical-class
Products
As is our custom for this list, CVEs that apply to more than one product family are counted once for each family they affect. We note, by the way, that CVE names don’t always reflect affected product families closely. In particular, some CVEs names in the Office family may mention products that don’t appear in the list of products affected by the CVE, and vice versa.
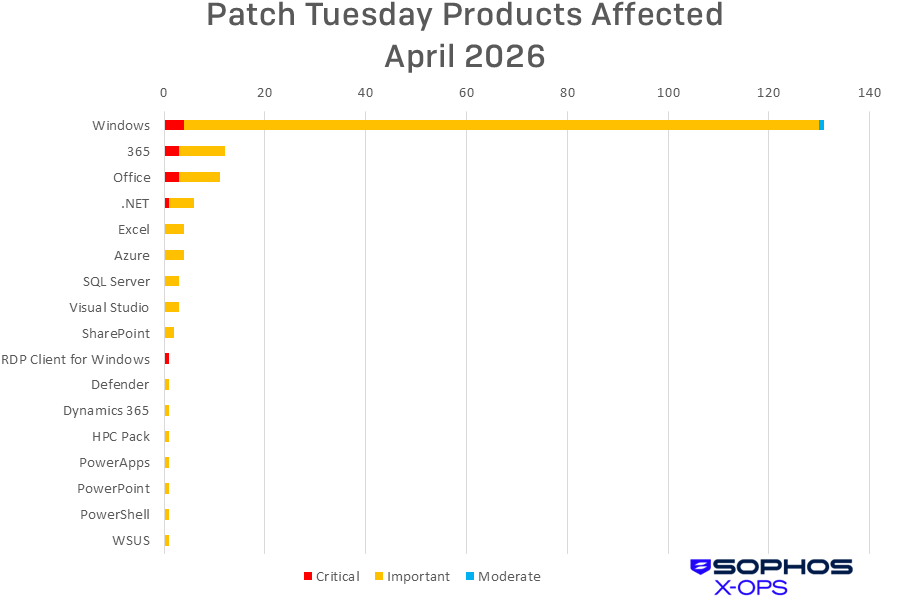
Figure 2: Windows dominates the patch list, though just four of those are Critical-class issues
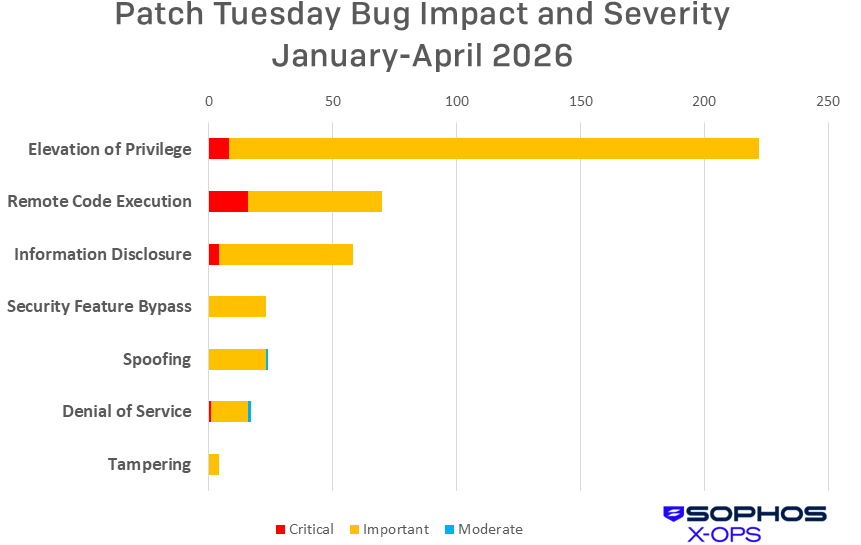
Figure 3: Over the years we have flagged repeatedly that April and October, and to a lesser extent January, tend to be high-load patch months. As 2026 unfolds, we’ll be keeping an eye on overall patch counts, but for now, we’ll simply note that the cumulative EoP total alone went up by 73 percent in April. The rest of 2026 might be quite a ride.
Notable April updates
In addition to the issues discussed above, a number of specific items merit attention.
CVE-2026-33824 — Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution
A Critical-severity RCE with a punishing 9.8 CVSS Base score, it’s a bit of a relief that Microsoft apparently found this one in-house rather than in the wild. The problem rests in Internet Key Exchange, the secure key-management protocol that negotiates secure IPsec associations – so, affecting great swaths of connectivity. This one comes with temporary mitigation options: If you cannot immediately install this update, adjust your traffic rules for UDP ports 500 and 4500 – blocking inbound traffic for systems that don’t use IKE, or configuring the ports to accept inbound traffic only from known peer addresses for systems that do. (There is a fine post on WindowsForum that discusses this bug and how to parse Microsoft’s guidance concerning it.) But do install this patch as soon as you can.
CVE-2026-32201 — Microsoft SharePoint Server Spoofing Vulnerability
A true in-the-wild zero-day before getting its Patch Tuesday comeuppance, this bug would permit an unauthorized attacker to spoof an actual user, able to read or modify certain data and potentially adding heft to social-engineering trickery. It rates only an Important severity (or, if you prefer, a CVSS Base score of 6.5), but Microsoft confirms that it’s in active use. Prioritize your patching accordingly.
CVE-2026-33825 — Microsoft Defender Elevation of Privilege Vulnerability
The only vulnerability publicly disclosed in advance of Patch Tuesday, this Important-severity EoP would allow an attacker to elevate privileges locally if Defender is enabled. Microsoft customers who have Defender enabled and take their automatic updates will be patched automatically, or can manually draw down the update if they don’t want to wait. Meanwhile, systems on which Defender is disabled cannot be exploited by this vulnerability.
CVE-2026-32190 — Microsoft PowerPoint Remote Code Execution Vulnerability
CVE-2026-33114 — Microsoft Word Remote Code Execution Vulnerability
CVE-2026-33115 — Microsoft Word Remote Code Execution Vulnerability
Office and 365 share three Critical-severity vulnerabilities this month; all three include Preview Pane as a vector.
CVE-2026-26151 — Remote Desktop Spoofing Vulnerability
An excellent development: Starting this month, the Remote Desktop Connection app shows new security warnings when you open RDP files. This CVE makes that possible — it literally beefs up the user interface’s warning of potentially dangerous operations. (Microsoft has the details on their site.) Considering RDP’s long reign atop the initial-attacker-access charts, it’s good to add some friction to the process.
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS |
Sophos XGS Firewall |
| CVE-2026-26169 | Exp/2626169-A | Exp/2626169-A |
| CVE-2026-27908 | Exp/2627908-A | Exp/2627908-A |
| CVE-2026-27909 | Exp/2627909-A | Exp/2627909-A |
| CVE-2026-27914 | Exp/2627914-A | Exp/2627914-A |
| CVE-2026-27921 | Exp/2627921-A | Exp/2627921-A |
| CVE-2026-32070 | Exp/2632070-A | Exp/2632070-A |
| CVE-2026-32093 | Exp/2632093-A | Exp/2632093-A |
| CVE-2026-32152 | Exp/2632152-A | Exp/2632152-A |
| CVE-2026-32154 | Exp/2632154-A | Exp/2632154-A |
| CVE-2026-32162 | Exp/2632162-A | Exp/2632162-A |
| CVE-2026-32201 | SID:2312418 | SID:2312418 |
| CVE-2026-32202 | SID:2312387, Troj/JSExp-Y | SID:2312387, Troj/JSExp-Y |
| CVE-2026-33825 | SID:2312409, ATK/BHammer-A, ATK/BHammer-B, ATK/BHammer-C | SID:2312409, ATK/BHammer-A, ATK/BHammer-B, ATK/BHammer-C |
| CVE-2026-33826 | sid:2312419 | sid:2312419 |
| CVE-2026-34621 (Adobe) | Troj/PDF-BG |
Troj/PDF-BG
|
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of April patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE.
Elevation of Privilege (94 CVEs)
| Important severity | |
| CVE-2026-20930 | Windows Management Services Elevation of Privilege Vulnerability |
| CVE-2026-25184 | Applocker Filter Driver (applockerfltr.sys) Elevation of Privilege Vulnerability |
| CVE-2026-26152 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability |
| CVE-2026-26153 | Windows Encrypted File System (EFS) Elevation of Privilege Vulnerability |
| CVE-2026-26159 | Remote Desktop Client Elevation of Privilege Vulnerability |
| CVE-2026-26160 | Remote Desktop Licensing Service Elevation of Privilege Vulnerability |
| CVE-2026-26161 | Windows Sensor Data Service Elevation of Privilege Vulnerability |
| CVE-2026-26162 | Windows OLE Elevation of Privilege Vulnerability |
| CVE-2026-26163 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-26165 | Windows Shell Elevation of Privilege Vulnerability |
| CVE-2026-26166 | Windows Shell Elevation of Privilege Vulnerability |
| CVE-2026-26167 | Windows Push Notifications Elevation of Privilege Vulnerability |
| CVE-2026-26168 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26170 | PowerShell Elevation of Privilege Vulnerability |
| CVE-2026-26172 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-26173 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26174 | Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability |
| CVE-2026-26176 | Windows Client Side Caching driver (csc.sys) Elevation of Privilege Vulnerability |
| CVE-2026-26177 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26178 | Windows Advanced Rasterization Platform Elevation of Privilege Vulnerability |
| CVE-2026-26179 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-26180 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-26181 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-26182 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26183 | Remote Access Management service/API (RPC server) Elevation of Privilege Vulnerability |
| CVE-2026-26184 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-27907 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability |
| CVE-2026-27908 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability |
| CVE-2026-27909 | Windows Search Service Elevation of Privilege Vulnerability |
| CVE-2026-27910 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2026-27911 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-27912 | Windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2026-27914 | Microsoft Management Console Elevation of Privilege Vulnerability |
| CVE-2026-27915 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27916 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27917 | Windows WFP NDIS Lightweight Filter Driver (wfplwfs.sys) Elevation of Privilege Vulnerability |
| CVE-2026-27918 | Windows Shell Elevation of Privilege Vulnerability |
| CVE-2026-27919 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27920 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27921 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability |
| CVE-2026-27922 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-27923 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-27924 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-27926 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-27927 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-27929 | Windows LUA File Virtualization Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-32068 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability |
| CVE-2026-32069 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-32070 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-32073 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-32074 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-32075 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-32076 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability |
| CVE-2026-32077 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-32078 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-32080 | Windows WalletService Elevation of Privilege Vulnerability |
| CVE-2026-32082 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability |
| CVE-2026-32083 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability |
| CVE-2026-32086 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32087 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32089 | Windows Speech Brokered Api Elevation of Privilege Vulnerability |
| CVE-2026-32090 | Windows Speech Brokered Api Elevation of Privilege Vulnerability |
| CVE-2026-32091 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-32093 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32150 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32152 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32153 | Windows Speech Runtime Elevation of Privilege Vulnerability |
| CVE-2026-32154 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32155 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32158 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-32159 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-32160 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-32162 | Windows COM Elevation of Privilege Vulnerability |
| CVE-2026-32163 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-32164 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-32165 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-32167 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-32168 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2026-32171 | Azure Logic Apps Elevation of Privilege Vulnerability |
| CVE-2026-32176 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-32184 | Microsoft High Performance Compute (HPC) Pack Elevation of Privilege Vulnerability |
| CVE-2026-32192 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2026-32195 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-32216 | Windows Redirected Drive Buffering System Elevation of Privilege Vulnerability |
| CVE-2026-32219 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-32222 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-32223 | Windows USB Printing Stack (usbprint.sys) Elevation of Privilege Vulnerability |
| CVE-2026-32224 | Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability |
| CVE-2026-33098 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-33099 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-33100 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-33101 | Windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2026-33104 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-33825 | Microsoft Defender Elevation of Privilege Vulnerability |
Remote Code Execution (20 CVEs)
| Critical severity | |
| CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability |
| CVE-2026-32190 | Microsoft PowerPoint Remote Code Execution Vulnerability |
| CVE-2026-33114 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-33115 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability |
| CVE-2026-33826 | Windows Active Directory Remote Code Execution Vulnerability |
| CVE-2026-33827 | Windows TCP/IP Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-23657 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-26156 | Windows Hyper-V Remote Code Execution Vulnerability |
| CVE-2026-32149 | Windows Hyper-V Remote Code Execution Vulnerability |
| CVE-2026-32156 | Windows UPnP Device Host Remote Code Execution Vulnerability |
| CVE-2026-32183 | Windows Snipping Tool Remote Code Execution Vulnerability |
| CVE-2026-32189 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32197 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32198 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32199 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32200 | Microsoft PowerPoint Remote Code Execution Vulnerability |
| CVE-2026-32221 | Windows Graphics Component Remote Code Execution Vulnerability |
| CVE-2026-33095 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-33120 | Microsoft SQL Server Remote Code Execution Vulnerability |
Information Disclosure (20 CVEs)
| Important severity | |
| CVE-2026-20806 | Windows COM Server Information Disclosure Vulnerability |
| CVE-2026-23653 | GitHub Copilot and Visual Studio Code Information Disclosure Vulnerability |
| CVE-2026-26155 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability |
| CVE-2026-26169 | Windows Kernel Memory Information Disclosure Vulnerability |
| CVE-2026-27925 | Windows UPnP Device Host Information Disclosure Vulnerability |
| CVE-2026-27930 | Windows GDI Information Disclosure Vulnerability |
| CVE-2026-27931 | Windows GDI Information Disclosure Vulnerability |
| CVE-2026-32079 | Windows File Explorer Information Disclosure Vulnerability |
| CVE-2026-32081 | Package Catalog Information Disclosure Vulnerability |
| CVE-2026-32084 | Windows File Explorer Information Disclosure Vulnerability |
| CVE-2026-32085 | Remote Procedure Call Information Disclosure Vulnerability |
| CVE-2026-32151 | Windows Shell Information Disclosure Vulnerability |
| CVE-2026-32188 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-32212 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability |
| CVE-2026-32214 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability |
| CVE-2026-32215 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2026-32217 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2026-32218 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2026-33103 | Microsoft Dynamics 365 (On-Premises) Information Disclosure Vulnerability |
| CVE-2026-33822 | Microsoft Word Information Disclosure Vulnerability |
Security Feature Bypass (12 CVEs)
| Important severity | |
| CVE-2026-0390 | UEFI Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-20928 | Windows Recovery Environment Security Feature Bypass Vulnerability |
| CVE-2026-23670 | Windows Virtualization-Based Security (VBS) Security Feature Bypass Vulnerability |
| CVE-2026-26143 | Microsoft PowerShell Security Feature Bypass Vulnerability |
| CVE-2026-26149 | Microsoft Power Apps Security Feature Bypass |
| CVE-2026-26175 | Windows Boot Manager Security Feature Bypass Vulnerability |
| CVE-2026-27906 | Windows Hello Security Feature Bypass Vulnerability |
| CVE-2026-27913 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-27928 | Windows Hello Security Feature Bypass Vulnerability |
| CVE-2026-32088 | Windows Biometric Service Security Feature Bypass Vulnerability |
| CVE-2026-32220 | Windows Virtualization-Based Security (VBS) Security Feature Bypass Vulnerability |
| CVE-2026-32225 | Windows Shell Security Feature Bypass Vulnerability |
Denial of Service (8 CVEs)
| Critical severity | |
| CVE-2026-23666 | .NET Framework Denial of Service Vulnerability |
| Important severity | |
| CVE-2026-26171 | .NET Denial of Service Vulnerability |
| CVE-2026-32071 | Windows Local Security Authority Subsystem Service (LSASS) Denial of Service Vulnerability |
| CVE-2026-32181 | Connected User Experiences and Telemetry Service Denial of Service Vulnerability |
| CVE-2026-32203 | .NET and Visual Studio Denial of Service Vulnerability |
| CVE-2026-32226 | .NET Framework Denial of Service Vulnerability |
| CVE-2026-33096 | HTTP.sys Denial of Service Vulnerability |
| CVE-2026-33116 | .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability |
Spoofing (8 CVEs)
| Important severity | |
| CVE-2026-20945 | Microsoft SharePoint Server Spoofing Vulnerability |
| CVE-2026-26151 | Remote Desktop Spoofing Vulnerability |
| CVE-2026-32072 | Active Directory Spoofing Vulnerability |
| CVE-2026-32178 | .NET Spoofing Vulnerability |
| CVE-2026-32196 | Windows Admin Center in Azure Portal Spoofing Vulnerability |
| CVE-2026-32201 | Microsoft SharePoint Server Spoofing Vulnerability |
| CVE-2026-32202 | Windows Shell Spoofing Vulnerability |
| Moderate severity | |
| CVE-2026-33829 | Windows Snipping Tool Spoofing Vulnerability |
Tampering (1 CVE)
| Important severity | |
| CVE-2026-26154 | Windows Server Update Service (WSUS) Tampering Vulnerability |
Appendix B: Exploitability and CVSS
One CVE in April is known to be already under exploit in the wild.
| Exploit detected | |
| CVE-2026-32201 | Microsoft SharePoint Server Spoofing Vulnerability |
This is a list of the 24 April CVEs judged by Microsoft to be more likely to be exploited in the wild within the first 30 days post-release. The list is arranged by CVE.
| Exploitation more likely within the next 30 days | |
| CVE-2026-0390 | UEFI Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-26151 | Remote Desktop Spoofing Vulnerability |
| CVE-2026-26169 | Windows Kernel Memory Information Disclosure Vulnerability |
| CVE-2026-26173 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26177 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26182 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-27906 | Windows Hello Security Feature Bypass Vulnerability |
| CVE-2026-27908 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability |
| CVE-2026-27909 | Windows Search Service Elevation of Privilege Vulnerability |
| CVE-2026-27913 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-27914 | Microsoft Management Console Elevation of Privilege Vulnerability |
| CVE-2026-27921 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability |
| CVE-2026-32070 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-32075 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-32093 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32152 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32154 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32155 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32162 | Windows COM Elevation of Privilege Vulnerability |
| CVE-2026-32202 | Windows Shell Spoofing Vulnerability |
| CVE-2026-32225 | Windows Shell Security Feature Bypass Vulnerability |
| CVE-2026-33104 | Win32k Elevation of Privilege Vulnerability |
| CVE-2026-33825 | Microsoft Defender Elevation of Privilege Vulnerability |
| CVE-2026-33826 | Windows Active Directory Remote Code Execution Vulnerability |
These are the April CVEs with a Microsoft-assessed CVSS Base score of 8.0 or higher. They are arranged by score and further sorted by CVE. For more information on how CVSS works, please see our series on patch prioritization schema.
| CVSS Base | CVSS Temporal | CVE | Title |
| 9.8 | 8.5 | CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability |
| 9.0 | 7.9 | CVE-2026-26149 | Microsoft Power Apps Security Feature Bypass |
| 8.8 | 7.7 | CVE-2026-26167 | Windows Push Notifications Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-26178 | Windows Advanced Rasterization Platform Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability |
| 8.8 | 7.7 | CVE-2026-32171 | Azure Logic Apps Elevation of Privilege Vulnerability |
| 8.8 | 7.7 | CVE-2026-32225 | Windows Shell Security Feature Bypass Vulnerability |
| 8.8 | 7.7 | CVE-2026-33120 | Microsoft SQL Server Remote Code Execution Vulnerability |
| 8.7 | 7.6 | CVE-2026-27928 | Windows Hello Security Feature Bypass Vulnerability |
| 8.4 | 7.3 | CVE-2026-32091 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| 8.4 | 7.3 | CVE-2026-32162 | Windows COM Elevation of Privilege Vulnerability |
| 8.4 | 7.3 | CVE-2026-32190 | Microsoft PowerPoint Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-32221 | Windows Graphics Component Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-33114 | Microsoft Word Remote Code Execution Vulnerability |
| 8.4 | 7.3 | CVE-2026-33115 | Microsoft Word Remote Code Execution Vulnerability |
| 8.1 | 7.1 | CVE-2026-33827 | Windows TCP/IP Remote Code Execution Vulnerability |
| 8.0 | 7.0 | CVE-2026-27912 | Windows Kerberos Elevation of Privilege Vulnerability |
| 8.0 | 7.0 | CVE-2026-33826 | Windows Active Directory Remote Code Execution Vulnerability |
Appendix C: Products Affected
This is a list of April’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE. Patches that are shared among multiple product families are listed multiple131 times, once for each product family. Certain issues for which advisories have been issued are covered in Appendix D, and issues affecting Windows Server are further sorted in Appendix E. All CVE titles are accurate as made available by Microsoft. For further information on why certain products may appear in titles and not product families (or vice versa), please consult Microsoft.
Windows (131 CVEs)
| Critical severity | |
| CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability |
| CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability |
| CVE-2026-33826 | Windows Active Directory Remote Code Execution Vulnerability |
| CVE-2026-33827 | Windows TCP/IP Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-0390 | UEFI Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-20806 | Windows COM Server Information Disclosure Vulnerability |
| CVE-2026-20928 | Windows Recovery Environment Security Feature Bypass Vulnerability |
| CVE-2026-20930 | Windows Management Services Elevation of Privilege Vulnerability |
| CVE-2026-23670 | Windows Virtualization-Based Security (VBS) Security Feature Bypass Vulnerability |
| CVE-2026-25184 | Applocker Filter Driver (applockerfltr.sys) Elevation of Privilege Vulnerability |
| CVE-2026-26151 | Remote Desktop Spoofing Vulnerability |
| CVE-2026-26152 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability |
| CVE-2026-26153 | Windows Encrypted File System (EFS) Elevation of Privilege Vulnerability |
| CVE-2026-26154 | Windows Server Update Service (WSUS) Tampering Vulnerability |
| CVE-2026-26155 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability |
| CVE-2026-26156 | Windows Hyper-V Remote Code Execution Vulnerability |
| CVE-2026-26159 | Remote Desktop Client Elevation of Privilege Vulnerability |
| CVE-2026-26160 | Remote Desktop Licensing Service Elevation of Privilege Vulnerability |
| CVE-2026-26161 | Windows Sensor Data Service Elevation of Privilege Vulnerability |
| CVE-2026-26162 | Windows OLE Elevation of Privilege Vulnerability |
| CVE-2026-26163 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-26165 | Windows Shell Elevation of Privilege Vulnerability |
| CVE-2026-26166 | Windows Shell Elevation of Privilege Vulnerability |
| CVE-2026-26167 | Windows Push Notifications Elevation of Privilege Vulnerability |
| CVE-2026-26168 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26169 | Windows Kernel Memory Information Disclosure Vulnerability |
| CVE-2026-26170 | PowerShell Elevation of Privilege Vulnerability |
| CVE-2026-26172 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-26173 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26174 | Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability |
| CVE-2026-26175 | Windows Boot Manager Security Feature Bypass Vulnerability |
| CVE-2026-26176 | Windows Client Side Caching driver (csc.sys) Elevation of Privilege Vulnerability |
| CVE-2026-26177 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26178 | Windows Advanced Rasterization Platform Elevation of Privilege Vulnerability |
| CVE-2026-26179 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-26180 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-26181 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-26182 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-26183 | Remote Access Management service/API (RPC server) Elevation of Privilege Vulnerability |
| CVE-2026-26184 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-27906 | Windows Hello Security Feature Bypass Vulnerability |
| CVE-2026-27907 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability |
| CVE-2026-27908 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability |
| CVE-2026-27909 | Windows Search Service Elevation of Privilege Vulnerability |
| CVE-2026-27910 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2026-27911 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-27912 | Windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2026-27913 | Secure Boot Security Feature Bypass Vulnerability |
| CVE-2026-27914 | Microsoft Management Console Elevation of Privilege Vulnerability |
| CVE-2026-27915 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27916 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27917 | Windows WFP NDIS Lightweight Filter Driver (wfplwfs.sys) Elevation of Privilege Vulnerability |
| CVE-2026-27918 | Windows Shell Elevation of Privilege Vulnerability |
| CVE-2026-27919 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27920 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-27921 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability |
| CVE-2026-27922 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-27923 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-27924 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-27925 | Windows UPnP Device Host Information Disclosure Vulnerability |
| CVE-2026-27926 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-27927 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-27928 | Windows Hello Security Feature Bypass Vulnerability |
| CVE-2026-27929 | Windows LUA File Virtualization Filter Driver Elevation of Privilege Vulnerability |
| CVE-2026-27930 | Windows GDI Information Disclosure Vulnerability |
| CVE-2026-27931 | Windows GDI Information Disclosure Vulnerability |
| CVE-2026-32068 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability |
| CVE-2026-32069 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-32070 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2026-32071 | Windows Local Security Authority Subsystem Service (LSASS) Denial of Service Vulnerability |
| CVE-2026-32072 | Active Directory Spoofing Vulnerability |
| CVE-2026-32073 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-32074 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-32075 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-32076 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability |
| CVE-2026-32077 | Windows UPnP Device Host Elevation of Privilege Vulnerability |
| CVE-2026-32078 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-32079 | Windows File Explorer Information Disclosure Vulnerability |
| CVE-2026-32080 | Windows WalletService Elevation of Privilege Vulnerability |
| CVE-2026-32081 | Package Catalog Information Disclosure Vulnerability |
| CVE-2026-32082 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability |
| CVE-2026-32083 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability |
| CVE-2026-32084 | Windows File Explorer Information Disclosure Vulnerability |
| CVE-2026-32085 | Remote Procedure Call Information Disclosure Vulnerability |
| CVE-2026-32086 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32087 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32088 | Windows Biometric Service Security Feature Bypass Vulnerability |
| CVE-2026-32089 | Windows Speech Brokered Api Elevation of Privilege Vulnerability |
| CVE-2026-32090 | Windows Speech Brokered Api Elevation of Privilege Vulnerability |
| CVE-2026-32091 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-32093 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32149 | Windows Hyper-V Remote Code Execution Vulnerability |
| CVE-2026-32150 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability |
| CVE-2026-32151 | Windows Shell Information Disclosure Vulnerability |
| CVE-2026-32152 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32153 | Windows Speech Runtime Elevation of Privilege Vulnerability |
| CVE-2026-32154 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32155 | Desktop Window Manager Elevation of Privilege Vulnerability |
| CVE-2026-32156 | Windows UPnP Device Host Remote Code Execution Vulnerability |
| CVE-2026-32158 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-32159 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-32160 | Windows Push Notifications Apps Elevation of Privilege Vulnerability |
| CVE-2026-32162 | Windows COM Elevation of Privilege Vulnerability |
| CVE-2026-32163 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-32164 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-32165 | Windows User Interface Core Elevation of Privilege Vulnerability |
| CVE-2026-32181 | Connected User Experiences and Telemetry Service Denial of Service Vulnerability |
| CVE-2026-32183 | Windows Snipping Tool Remote Code Execution Vulnerability |
| CVE-2026-32195 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2026-32202 | Windows Shell Spoofing Vulnerability |
| CVE-2026-32212 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability |
| CVE-2026-32214 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability |
| CVE-2026-32215 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2026-32216 | Windows Redirected Drive Buffering System Elevation of Privilege Vulnerability |
| CVE-2026-32217 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2026-32218 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2026-32219 | Microsoft Brokering File System Elevation of Privilege Vulnerability |
| CVE-2026-32220 | Windows Virtualization-Based Security (VBS) Security Feature Bypass Vulnerability |
| CVE-2026-32221 | Windows Graphics Component Remote Code Execution Vulnerability |
| CVE-2026-32222 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2026-32223 | Windows USB Printing Stack (usbprint.sys) Elevation of Privilege Vulnerability |
| CVE-2026-32225 | Windows Shell Security Feature Bypass Vulnerability |
| CVE-2026-33096 | HTTP.sys Denial of Service Vulnerability |
| CVE-2026-33098 | Windows Projected File System Elevation of Privilege Vulnerability |
| CVE-2026-33099 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-33100 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2026-33101 | Windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2026-33104 | Win32k Elevation of Privilege Vulnerability |
| Moderate severity | |
| CVE-2026-33829 | Windows Snipping Tool Spoofing Vulnerability |
365 (12 CVEs)
| Critical severity | |
| CVE-2026-32190 | Microsoft PowerPoint Remote Code Execution Vulnerability |
| CVE-2026-33114 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-33115 | Microsoft Word Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-23657 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-32188 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-32189 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32197 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32198 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32199 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32200 | Microsoft PowerPoint Remote Code Execution Vulnerability |
| CVE-2026-33095 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-33822 | Microsoft Word Information Disclosure Vulnerability |
Office (11 CVEs)
| Critical severity | |
| CVE-2026-32190 | Microsoft PowerPoint Remote Code Execution Vulnerability |
| CVE-2026-33114 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-33115 | Microsoft Word Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2026-23657 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2026-32188 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-32189 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32197 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32198 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32199 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32200 | Microsoft PowerPoint Remote Code Execution Vulnerability |
| CVE-2026-33095 | Microsoft Word Remote Code Execution Vulnerability |
.NET (6 CVEs)
| Critical severity | |
| CVE-2026-23666 | .NET Framework Denial of Service Vulnerability |
| Important severity | |
| CVE-2026-26171 | .NET Denial of Service Vulnerability |
| CVE-2026-32226 | .NET Framework Denial of Service Vulnerability |
| CVE-2026-33116 | .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability |
| CVE-2026-32178 | .NET Spoofing Vulnerability |
| CVE-2026-32203 | .NET and Visual Studio Denial of Service Vulnerability |
Excel (5 CVEs)
| Important severity | |
| CVE-2026-32188 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2026-32189 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32197 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32198 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2026-32199 | Microsoft Excel Remote Code Execution Vulnerability |
Azure (4 CVEs)
| Important severity | |
| CVE-2026-32168 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2026-32171 | Azure Logic Apps Elevation of Privilege Vulnerability |
| CVE-2026-32192 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2026-32196 | Windows Admin Center in Azure Portal Spoofing Vulnerability |
SQL Server (3 CVEs)
| Important severity | |
| CVE-2026-32167 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-32176 | SQL Server Elevation of Privilege Vulnerability |
| CVE-2026-33120 | Microsoft SQL Server Remote Code Execution Vulnerability |
Visual Studio (3 CVEs)
| Important severity | |
| CVE-2026-23653 | GitHub Copilot and Visual Studio Code Information Disclosure Vulnerability |
| CVE-2026-32178 | .NET Spoofing Vulnerability |
| CVE-2026-32203 | .NET and Visual Studio Denial of Service Vulnerability |
SharePoint (2 CVEs)
| Important severity | |
| CVE-2026-20945 | Microsoft SharePoint Server Spoofing Vulnerability |
| CVE-2026-32201 | Microsoft SharePoint Server Spoofing Vulnerability |
Defender (1 CVE)
| Important severity | |
| CVE-2026-33825 | Microsoft Defender Elevation of Privilege Vulnerability |
Dynamics 365 (1 CVE)
| Important severity | |
| CVE-2026-33103 | Microsoft Dynamics 365 (On-Premises) Information Disclosure Vulnerability |
HPC Pack (1 CVE)
| Important severity | |
| CVE-2026-32184 | Microsoft High Performance Compute (HPC) Pack Elevation of Privilege Vulnerability |
PowerApps (1 CVE)
| Important severity | |
| CVE-2026-26149 | Microsoft Power Apps Security Feature Bypass |
PowerPoint (1 CVE)
| Important severity | |
| CVE-2026-32200 | Microsoft PowerPoint Remote Code Execution Vulnerability |
PowerShell (1 CVE)
| Important severity | |
| CVE-2026-26143 | Microsoft PowerShell Security Feature Bypass Vulnerability |
RDP Client for Windows (1 CVE)
| Critical severity | |
| CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability |
Windows Server Update Services (WSUS) (1 CVE)
| Important severity | |
| CVE-2026-32224 | Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability |
Appendix D: Advisories and Other Products
There are 80 Edge-related advisories listed in April’s release, all but two from Chrome. Because the two from Microsoft were (like the Chrome CVEs) patched before Patch Tuesday, and because this post is already gruesomely long, we have massed all 80 together in the very long table below.
| CVE-2026-5272 | Chromium: CVE-2026-5272 Heap buffer overflow in GPU |
| CVE-2026-5273 | Chromium: CVE-2026-5273 Use after free in CSS |
| CVE-2026-5274 | Chromium: CVE-2026-5274 Integer overflow in Codecs |
| CVE-2026-5275 | Chromium: CVE-2026-5275 Heap buffer overflow in ANGLE |
| CVE-2026-5276 | Chromium: CVE-2026-5276 Insufficient policy enforcement in WebUSB |
| CVE-2026-5277 | Chromium: CVE-2026-5277 Integer overflow in ANGLE |
| CVE-2026-5279 | Chromium: CVE-2026-5279 Object corruption in V8 |
| CVE-2026-5280 | Chromium: CVE-2026-5280 Use after free in WebCodecs |
| CVE-2026-5281 | Chromium: CVE-2026-5281 Use after free in Dawn |
| CVE-2026-5283 | Chromium: CVE-2026-5283 Inappropriate implementation in ANGLE |
| CVE-2026-5284 | Chromium: CVE-2026-5284 Use after free in Dawn |
| CVE-2026-5285 | Chromium: CVE-2026-5285 Use after free in WebGL |
| CVE-2026-5286 | Chromium: CVE-2026-5286 Use after free in Dawn |
| CVE-2026-5287 | Chromium: CVE-2026-5287 Use after free in PDF |
| CVE-2026-5289 | Chromium: CVE-2026-5289 Use after free in Navigation |
| CVE-2026-5290 | Chromium: CVE-2026-5290 Use after free in Compositing |
| CVE-2026-5291 | Chromium: CVE-2026-5291 Inappropriate implementation in WebGL |
| CVE-2026-5292 | Chromium: CVE-2026-5292 Out of bounds read in WebCodecs |
| CVE-2026-5858 | Chromium: CVE-2026-5858 Heap buffer overflow in WebML |
| CVE-2026-5859 | Chromium: CVE-2026-5859 Integer overflow in WebML |
| CVE-2026-5860 | Chromium: CVE-2026-5860 Use after free in WebRTC |
| CVE-2026-5861 | Chromium: CVE-2026-5861 Use after free in V8 |
| CVE-2026-5862 | Chromium: CVE-2026-5862 Inappropriate implementation in V8 |
| CVE-2026-5863 | Chromium: CVE-2026-5863 Inappropriate implementation in V8 |
| CVE-2026-5864 | Chromium: CVE-2026-5864 Heap buffer overflow in WebAudio |
| CVE-2026-5865 | Chromium: CVE-2026-5865 Type Confusion in V8 |
| CVE-2026-5866 | Chromium: CVE-2026-5866 Use after free in Media |
| CVE-2026-5867 | Chromium: CVE-2026-5867 Heap buffer overflow in WebML |
| CVE-2026-5868 | Chromium: CVE-2026-5868 Heap buffer overflow in ANGLE |
| CVE-2026-5869 | Chromium: CVE-2026-5869 Heap buffer overflow in WebML |
| CVE-2026-5870 | Chromium: CVE-2026-5870 Integer overflow in Skia |
| CVE-2026-5871 | Chromium: CVE-2026-5871 Type Confusion in V8 |
| CVE-2026-5872 | Chromium: CVE-2026-5872 Use after free in Blink |
| CVE-2026-5873 | Chromium: CVE-2026-5873 Out of bounds read and write in V8 |
| CVE-2026-5874 | Chromium: CVE-2026-5874 Use after free in PrivateAI |
| CVE-2026-5875 | Chromium: CVE-2026-5875 Policy bypass in Blink |
| CVE-2026-5876 | Chromium: CVE-2026-5876 Side-channel information leakage in Navigation |
| CVE-2026-5877 | Chromium: CVE-2026-5877 Use after free in Navigation |
| CVE-2026-5878 | Chromium: CVE-2026-5878 Incorrect security UI in Blink |
| CVE-2026-5879 | Chromium: CVE-2026-5879 Insufficient validation of untrusted input in ANGLE |
| CVE-2026-5880 | Chromium: CVE-2026-5880 Incorrect security UI in browser UI |
| CVE-2026-5881 | Chromium: CVE-2026-5881 Policy bypass in LocalNetworkAccess |
| CVE-2026-5882 | Chromium: CVE-2026-5882 Incorrect security UI in Fullscreen |
| CVE-2026-5883 | Chromium: CVE-2026-5883 Use after free in Media |
| CVE-2026-5884 | Chromium: CVE-2026-5884 Insufficient validation of untrusted input in Media |
| CVE-2026-5885 | Chromium: CVE-2026-5885 Insufficient validation of untrusted input in WebML |
| CVE-2026-5886 | Chromium: CVE-2026-5886 Out of bounds read in WebAudio |
| CVE-2026-5887 | Chromium: CVE-2026-5887 Insufficient validation of untrusted input in Downloads |
| CVE-2026-5888 | Chromium: CVE-2026-5888 Uninitialized Use in WebCodecs |
| CVE-2026-5889 | Chromium: CVE-2026-5889 Cryptographic Flaw in PDFium |
| CVE-2026-5890 | Chromium: CVE-2026-5890 Race in WebCodecs |
| CVE-2026-5891 | Chromium: CVE-2026-5891 Insufficient policy enforcement in browser UI |
| CVE-2026-5892 | Chromium: CVE-2026-5892 Insufficient policy enforcement in PWAs |
| CVE-2026-5893 | Chromium: CVE-2026-5893 Race in V8 |
| CVE-2026-5894 | Chromium: CVE-2026-5894 Inappropriate implementation in PDF |
| CVE-2026-5895 | Chromium: CVE-2026-5895 Incorrect security UI in Omnibox |
| CVE-2026-5896 | Chromium: CVE-2026-5896 Policy bypass in Audio |
| CVE-2026-5897 | Chromium: CVE-2026-5897 Incorrect security UI in Downloads |
| CVE-2026-5898 | Chromium: CVE-2026-5898 Incorrect security UI in Omnibox |
| CVE-2026-5899 | Chromium: CVE-2026-5899 Incorrect security UI in History Navigation |
| CVE-2026-5900 | Chromium: CVE-2026-5900 Policy bypass in Downloads |
| CVE-2026-5901 | Chromium: CVE-2026-5901 Policy bypass in DevTools |
| CVE-2026-5902 | Chromium: CVE-2026-5902 Race in Media |
| CVE-2026-5903 | Chromium: CVE-2026-5903 Policy bypass in IFrameSandbox |
| CVE-2026-5904 | Chromium: CVE-2026-5904 Use after free in V8 |
| CVE-2026-5905 | Chromium: CVE-2026-5905 Incorrect security UI in Permissions |
| CVE-2026-5906 | Chromium: CVE-2026-5906 Incorrect security UI in Omnibox |
| CVE-2026-5907 | Chromium: CVE-2026-5907 Insufficient data validation in Media |
| CVE-2026-5908 | Chromium: CVE-2026-5908 Integer overflow in Media |
| CVE-2026-5909 | Chromium: CVE-2026-5909 Integer overflow in Media |
| CVE-2026-5910 | Chromium: CVE-2026-5910 Integer overflow in Media |
| CVE-2026-5911 | Chromium: CVE-2026-5911 Policy bypass in ServiceWorkers |
| CVE-2026-5912 | Chromium: CVE-2026-5912 Integer overflow in WebRTC |
| CVE-2026-5913 | Chromium: CVE-2026-5913 Out of bounds read in Blink |
| CVE-2026-5914 | Chromium: CVE-2026-5914 Type Confusion in CSS |
| CVE-2026-5915 | Chromium: CVE-2026-5915 Insufficient validation of untrusted input in WebML |
| CVE-2026-5918 | Chromium: CVE-2026-5918 Inappropriate implementation in Navigation |
| CVE-2026-5919 | Chromium: CVE-2026-5919 Insufficient validation of untrusted input in WebSockets |
| CVE-2026-33118 | Microsoft Edge (Chromium-based) Spoofing Vulnerability |
| CVE-2026-33119 | Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability |
Meanwhile, there are six updates from Adobe, all affecting ColdFusion 2025 – Update 6 and earlier versions, as well as ColdFusion 2023 – Update 18 and earlier versions. These are addresseḍ in APSB26-38. These are unrelated to the Adobe item covered in the Sophos protection noted above.
| CVE-2026-27282 | Improper Input Validation (CWE-20) |
| CVE-2026-27304 | Improper Input Validation (CWE-20) |
| CVE-2026-27305 | Improper Limitation of a Pathname to a Restricted Directory (‘Path Traversal’) (CWE-22) |
| CVE-2026-27306 | Improper Input Validation (CWE-20) |
| CVE-2026-27307 | Uncontrolled Resource Consumption (CWE-400) |
| CVE-2026-27308 | Uncontrolled Resource Consumption (CWE-400) |
Appendix E: Affected Windows Server versions
This is a table of 127 CVEs in the April release affecting Windows Server versions 2012 through 2025. The table differentiates among major versions of the platform but doesn’t go into deeper detail (eg., Server Core). An “x” indicates that the CVE does not apply to that version. CVE-2026-27906, CVE-2026-32153, CVE-2026-32195, and CVE-2026-32216 affect only client-side versions of Windows and are thus not included in the table. We do, however, include the two Important-severity, Windows-touching advisories from AMD and MITRE, since the Server versions they affect are known; those are indicated in this chart in blue.
Administrators are encouraged to use this appendix as a starting point to ascertain their specific exposure, as each reader’s situation, especially as it concerns products out of mainstream support, will vary. For specific Knowledge Base numbers, please consult Microsoft.
| CVE |
S-12 |
12r2 |
S-16 |
S-19 |
S-22 |
23h2 |
S-25 |
| CVE-2023-20585 |
× |
× |
× |
× |
× |
× |
■ |
| CVE-2026-0390 |
× |
× |
■ |
■ |
■ |
× |
× |
| CVE-2026-20806 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-20928 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-20930 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-23670 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-25184 |
× |
× |
× |
× |
× |
■ |
■ |
| CVE-2026-25250 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26151 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26152 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26153 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-26154 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26155 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26156 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26159 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26160 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26161 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-26162 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26163 |
× |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26165 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-26166 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-26167 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26168 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26169 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26170 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26172 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-26173 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26174 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26175 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-26176 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26177 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26178 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26179 |
× |
× |
× |
× |
× |
■ |
■ |
| CVE-2026-26180 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26181 |
× |
× |
× |
× |
× |
■ |
■ |
| CVE-2026-26182 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26183 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-26184 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-27907 |
× |
× |
× |
× |
× |
■ |
■ |
| CVE-2026-27908 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27909 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27910 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27911 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27912 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27913 |
■ |
■ |
■ |
■ |
■ |
■ |
× |
| CVE-2026-27914 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27915 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27916 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27917 |
× |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27918 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-27919 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27920 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27921 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27922 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27923 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27924 |
× |
× |
× |
× |
■ |
■ |
× |
| CVE-2026-27925 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27926 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-27927 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-27928 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27929 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27930 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-27931 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-32068 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32069 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32070 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32071 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32072 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32073 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32074 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32075 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32076 |
× |
× |
× |
× |
× |
■ |
■ |
| CVE-2026-32077 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32078 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32079 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32080 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32081 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32082 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32083 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32084 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32085 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32086 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32087 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32088 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32089 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32090 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32091 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32093 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32149 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32150 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32151 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32152 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-32154 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32155 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-32156 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32157 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32158 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32159 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32160 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32162 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32163 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32164 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32165 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32181 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-32183 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32202 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32212 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32214 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32215 |
× |
× |
× |
■ |
■ |
■ |
■ |
| CVE-2026-32217 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-32218 |
× |
× |
× |
× |
■ |
■ |
■ |
| CVE-2026-32219 |
× |
× |
× |
× |
× |
× |
■ |
| CVE-2026-32220 |
× |
× |
× |
× |
× |
× |
■ |
| CVE-2026-32221 |
× |
× |
× |
× |
× |
× |
■ |
| CVE-2026-32222 |
× |
× |
× |
× |
× |
× |
■ |
| CVE-2026-32223 |
× |
× |
× |
× |
× |
× |
■ |
| CVE-2026-32225 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-33096 |
× |
× |
× |
× |
× |
× |
■ |
| CVE-2026-33098 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-33099 |
■ |
■ |
■ |
■ |
■ |
■ |
× |
| CVE-2026-33100 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-33101 |
× |
× |
× |
× |
× |
■ |
■ |
| CVE-2026-33104 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-33824 |
× |
× |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-33826 |
× |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-33827 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
| CVE-2026-33829 |
■ |
■ |
■ |
■ |
■ |
■ |
■ |
Appendix F: Common Weakness Enumeration
As mentioned above, Microsoft now states which CWEs affect very nearly every CVE they address. (We noted only two CVEs that had no CWE information — CVE-2026-26149, the PowerApps security feature bypass, and the advisory-only CVE-2026-33118 affecting Edge/Chrome). We’re looking forward to analyzing this data over time.
This month, we decided to start off by seeing which CWEs were most heavily represented in this inaugural dataset. (For the moment, we’re not diving into specific CVE-CWE correlations — for instance, which CWEs are more prevalent among which product families — nor are we comparing prevalence of CWEs to seriousness of bugs, such as might be indicated by CVSS scores. Nor are we pointing out where the popular 2025 CWE Top 25 Most Dangerous Software Weaknesses List maps to April’s list.)
The April dataset of 163 patches references 196 CWEs. Of that 163, 29 patches referenced two CVEs, and five referenced three CWEs. Meanwhile, there were just 42 unique CWEs represented this month (the latest MITRE catalog, version 4.19.1, defines 944 total CWEs) and just three of those accounted for over half of all vulnerabilities patched in April, as shown in the table below.
| CWE | Count | CWE Name |
| CWE-416 | 56 | Use After Free |
| CWE-362 | 34 | Concurrent Execution using Shared Resource with Improper Synchronization (‘Race Condition’) |
| CWE-20 | 14 | Improper Input Validation |
| CWE-122 | 8 | Heap-based Buffer Overflow |
| CWE-125 | 8 | Out-of-bounds Read |
| CWE-822 | 8 | Untrusted Pointer Dereference |
| CWE-200 | 6 | Exposure of Sensitive Information to an Unauthorized Actor |
| CWE-415 | 6 | Double Free |
| CWE-284 | 5 | Improper Access Control |
| CWE-126 | 3 | Buffer Over-read |
| CWE-476 | 3 | NULL Pointer Dereference |
| CWE-532 | 3 | Insertion of Sensitive Information into Log File |
| CWE-77 | 2 | Improper Neutralization of Special Elements used in a Command (‘Command Injection’) |
| CWE-79 | 2 | Improper Neutralization of Input During Web Page Generation (‘Cross-site Scripting’) |
| CWE-89 | 2 | Improper Neutralization of Special Elements used in an SQL Command (‘SQL Injection’) |
| CWE-121 | 2 | Stack-based Buffer Overflow |
| CWE-191 | 2 | Integer Underflow (Wrap or Wraparound) |
| CWE-269 | 2 | Improper Privilege Management |
| CWE-306 | 2 | Missing Authentication for Critical Function |
| CWE-367 | 2 | Time-of-check Time-of-use (TOCTOU) Race Condition |
| CWE-400 | 2 | Uncontrolled Resource Consumption |
| CWE-502 | 2 | Deserialization of Untrusted Data |
| CWE-693 | 2 | Protection Mechanism Failure |
| CWE-843 | 2 | Access of Resource Using Incompatible Type (‘Type Confusion’) |
| CWE-59 | 1 | Improper Link Resolution Before File Access (‘Link Following’) |
| CWE-138 | 1 | Improper Neutralization of Special Elements |
| CWE-190 | 1 | Integer Overflow or Wraparound |
| CWE-212 | 1 | Improper Removal of Sensitive Information Before Storage or Transfer |
| CWE-280 | 1 | Improper Handling of Insufficient Permissions or Privileges |
| CWE-285 | 1 | Improper Authorization |
| CWE-287 | 1 | Improper Authentication |
| CWE-349 | 1 | Acceptance of Extraneous Untrusted Data With Trusted Data |
| CWE-357 | 1 | Insufficient UI Warning of Dangerous Operations |
| CWE-522 | 1 | Insufficiently Protected Credentials |
| CWE-611 | 1 | Improper Restriction of XML External Entity Reference |
| CWE-681 | 1 | Incorrect Conversion between Numeric Types |
| CWE-755 | 1 | Improper Handling of Exceptional Conditions |
| CWE-807 | 1 | Reliance on Untrusted Inputs in a Security Decision |
| CWE-835 | 1 | Loop with Unreachable Exit Condition (‘Infinite Loop’) |
| CWE-908 | 1 | Use of Uninitialized Resource |
| CWE-922 | 1 | Insecure Storage of Sensitive Information |
| CWE-1220 | 1 | Insufficient Granularity of Access Control |
Among the 29 CVEs that doubled up on their CWEs, the vast majority combined CWE-416 and CWE-362 – that is, a use-after-free plus a race condition. Though findings such as these are not exactly shocking for longtime observers, it’s exciting to have fresh statistics in hand as we contemplate whether the barn-busting April patch harvest is the shape of things to come.
Leave a Reply